Insights & updates from our experts
Prometheus Alertmanager Integration Guide
Prometheus is an open-source monitoring solution that resides locally on your machine.
What can Xurrent IMR do for Prometheus users?
With Prometheus's Integration, Xurrent IMR sends new Prometheus alerts to the right team and notifies them based on on-call schedules via email, text messages(SMS), phone calls(Voice), Slack, Microsoft Teams and iOS & Android push notifications, and escalates alerts until the alert is acknowledged or closed. Xurrent IMR provides your NOC, SRE and application engineers with detailed context around the Prometheus alert along with playbooks and a complete incident command framework to triage, remediate and resolve incidents with speed.
Whenever Prometheus alert rule condition is triggered, an alert is created in Xurrent IMR, which creates an incident. When that condition goes back to normal levels, Xurrent IMR will auto-resolve the incident.
You can also use Alert Rules to custom route specific Prometheus alerts to specific users, teams or escalation policies, write suppression rules, auto add notes, responders and incident tasks.
To integrate Prometheus with Xurrent IMR, complete the following steps:
In Xurrent IMR:
- To add a new Prometheus integration, go to Teams on Xurrent IMR and click on the team you want to add the integration to.
- Next, go to Services and click on the relevant Service.
- Go to Integrations and then Add New Integration. Give it a name and select the application Prometheus from the dropdown menu.
- Go to Configure under your Integrations and copy the Webhook URL generated.
In Prometheus:
- Ensure that both Prometheus and Prometheus Alertmanager are downloaded and accessible locally on your system. To download them, visit here
- Go to Alertmanager Folder and open alertmanager.yml. Add the webhook url (copied in the earlier steps) under Webhook Configs.
Your alertmanager.yml file should now look like this:
- Tip: If you're trying to generate alerts across multiple Xurrent IMR Services, you can define your Alert Rules in different files. For example: first_rules.yml, second_rules.yml, and so on, each with a different integration endpoint.
- In the Prometheus folder, open prometheus.yml. Add new rules files that you just created and set Target. Xurrent IMR groups Prometheus alerts based on the alertname parameter.
Your prometheus.yml file should look like this:
- Run Prometheus and Alert Manager using commands like:
run prometheus: ./prometheus --config.file=prometheus.ymlrun alertmanager: ./alertmanager --config.file=alertmanager.yml- Once Prometheus is running, you will be able to see the alerts rules you configured.
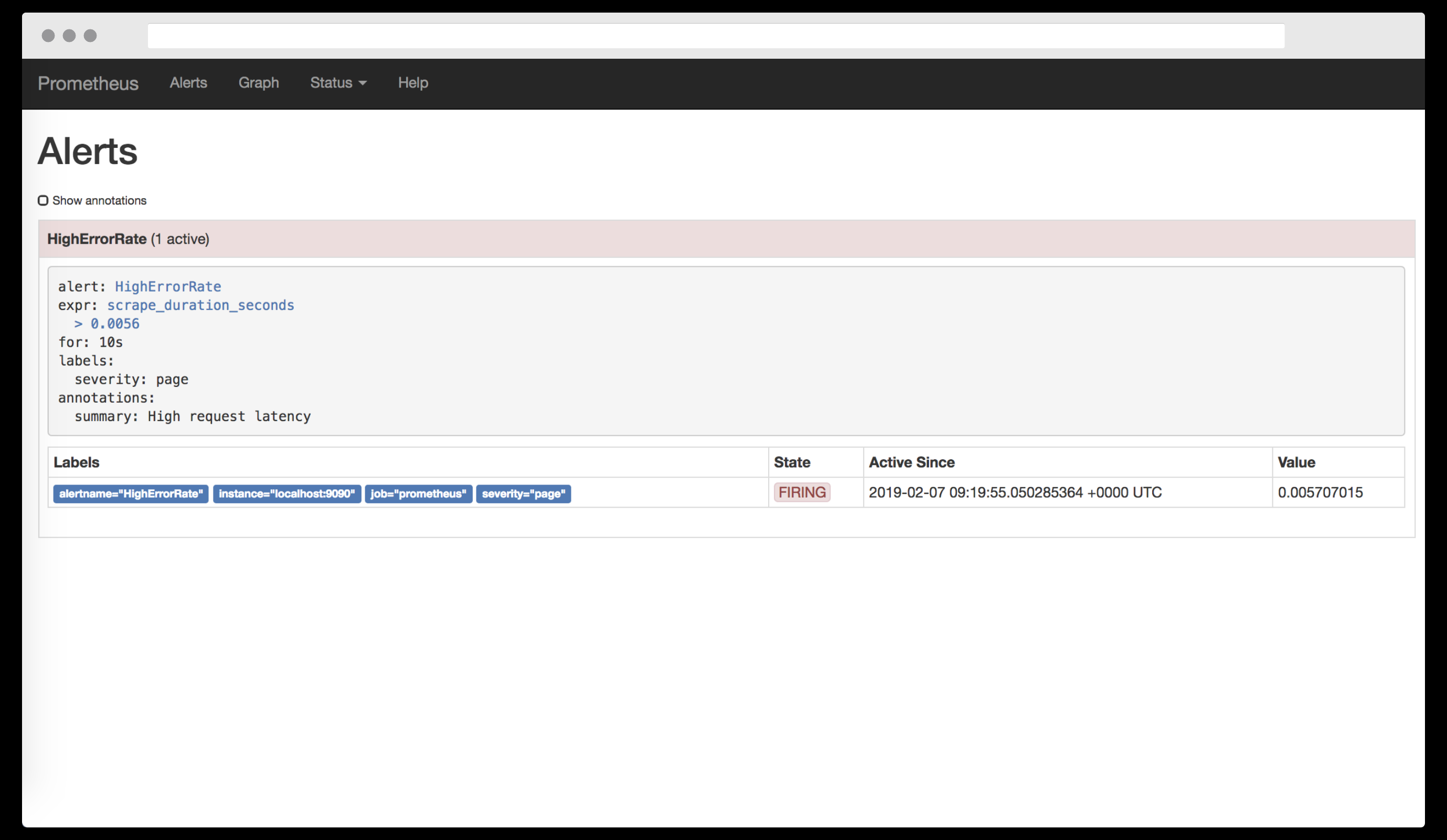
- When an alert is required, Xurrent IMR will automatically create an incident.
- Prometheus is now integrated.
For Prometheus Docker installations
In order to scrape data from the multiple services or pods, one has to write custom scraping rules on Prometheus. Refer to the example below.
In the above example, scrape_configs defines the location from where the data needs to be scraped, which in this case is the kubernetes apiserver. You can define multiple jobs to scrape data from different services or pods. For Prometheus scraping, you need to define prometheus.io/scrape: 'true', prometheus.io/port: '9100' within the annotations section for the service or pod.
/etc/prometheus/prometheus.rules is the location of the Prometheus rule file, an example of which is shown below:
In the above example, the different resource related partitions are defined in groups and these groups have different rules for alerting. You need to make sure that you add the appropriate labels in your rules because Xurrent IMR will be matching these labels in the Alertmanager settings.
Now if the rule breaks and Prometheus sends it to the Alertmanager, then alertmanger must have the appropriate channel to notify. For configurating Alertmanager with Xurrent IMR or Slack, please see the below example:
One can add proxy in global settings if needed, like the snippet below.
For more information, visit the Alertmanager docs here
















.jpg)