Insights & updates from our experts
Set up Azure AD as your SAML Identity Provider
Here's a walk-through of setting up Azure AD as your SAML Identity Provider. This allows your team to log into Xurrent IMR without a new email/password combination.
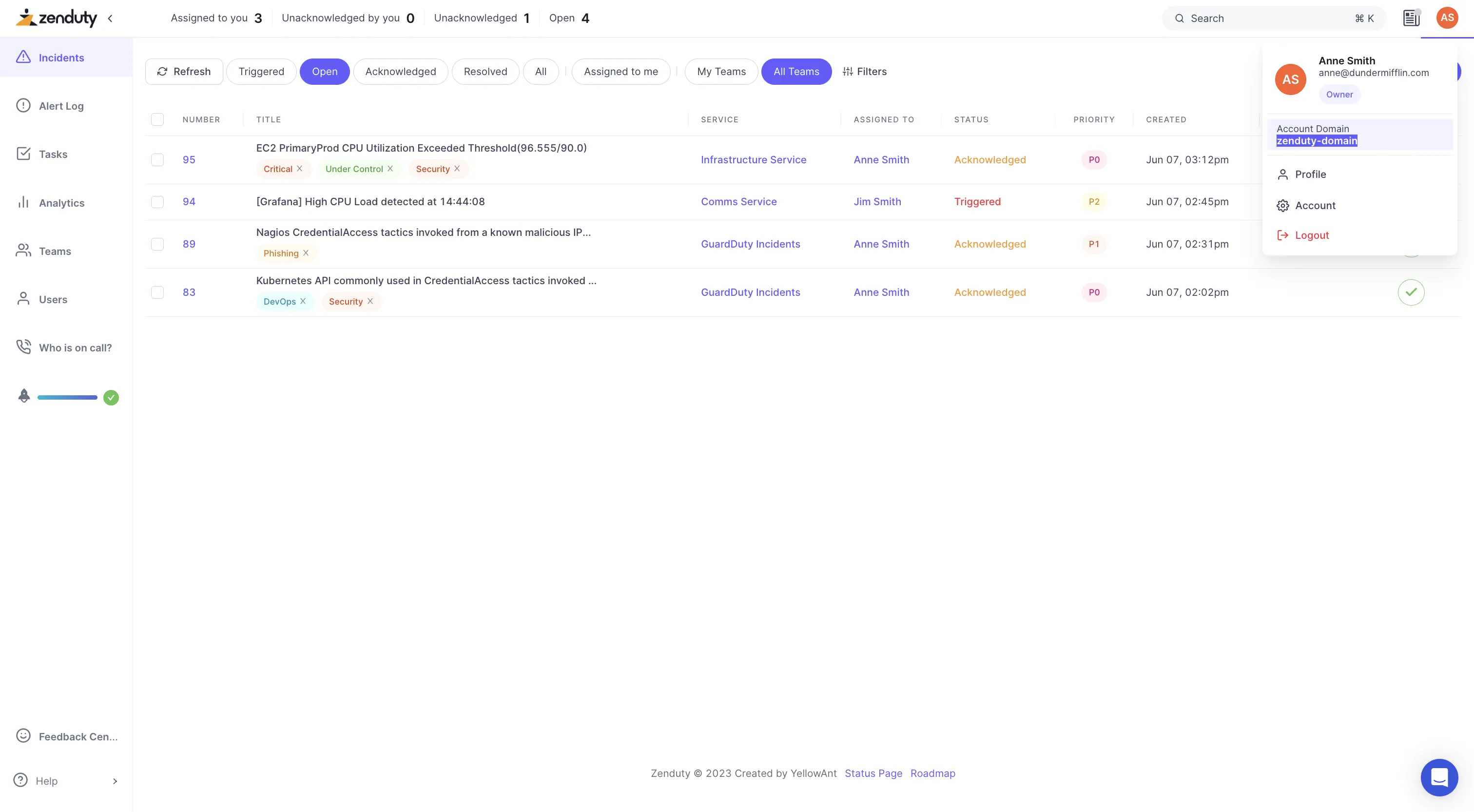
- Log in to Xurrent IMR as an account owner. In another tab, log into Azure as an administrator.
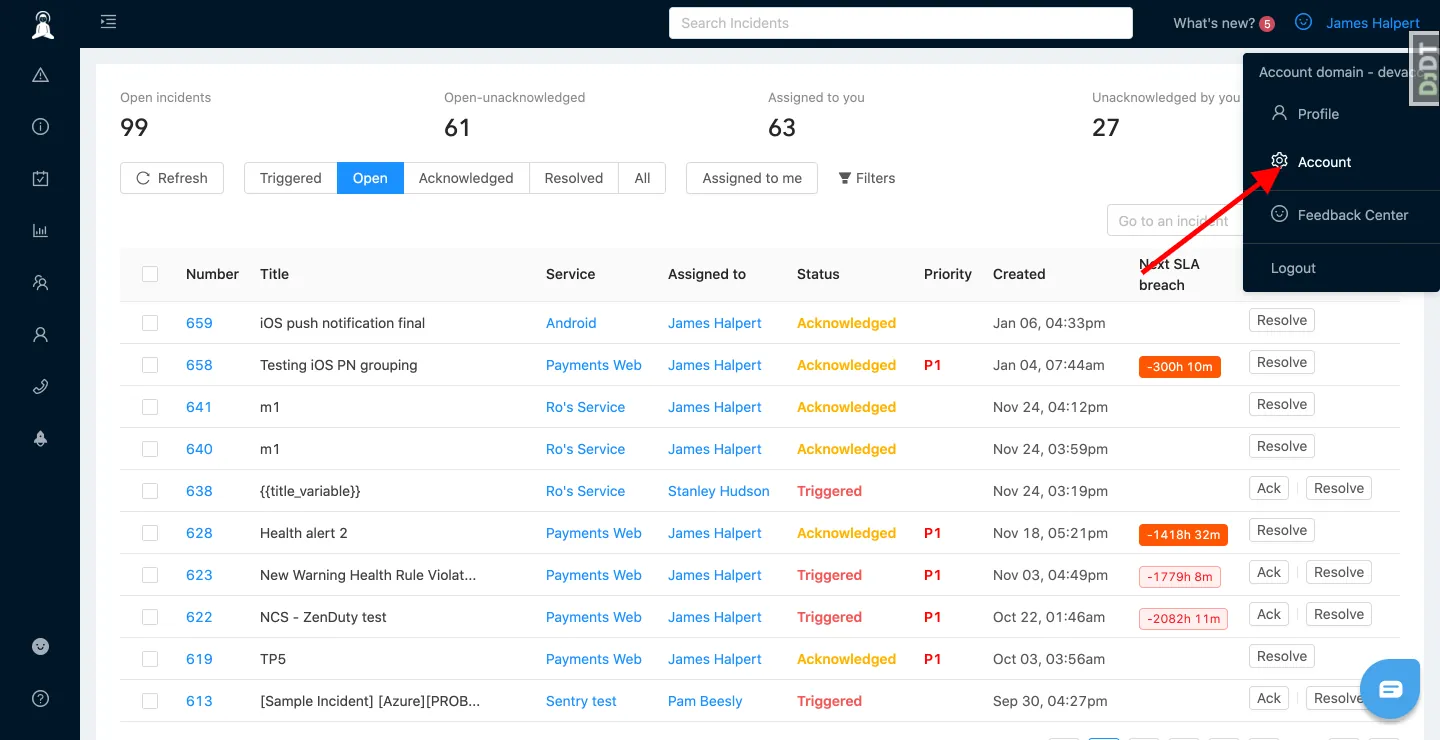
- In the Xurrent IMR tab, click on your name in the top right corner, which will reveal a dropdown with your account's domain name. Copy your account domain name for later use.
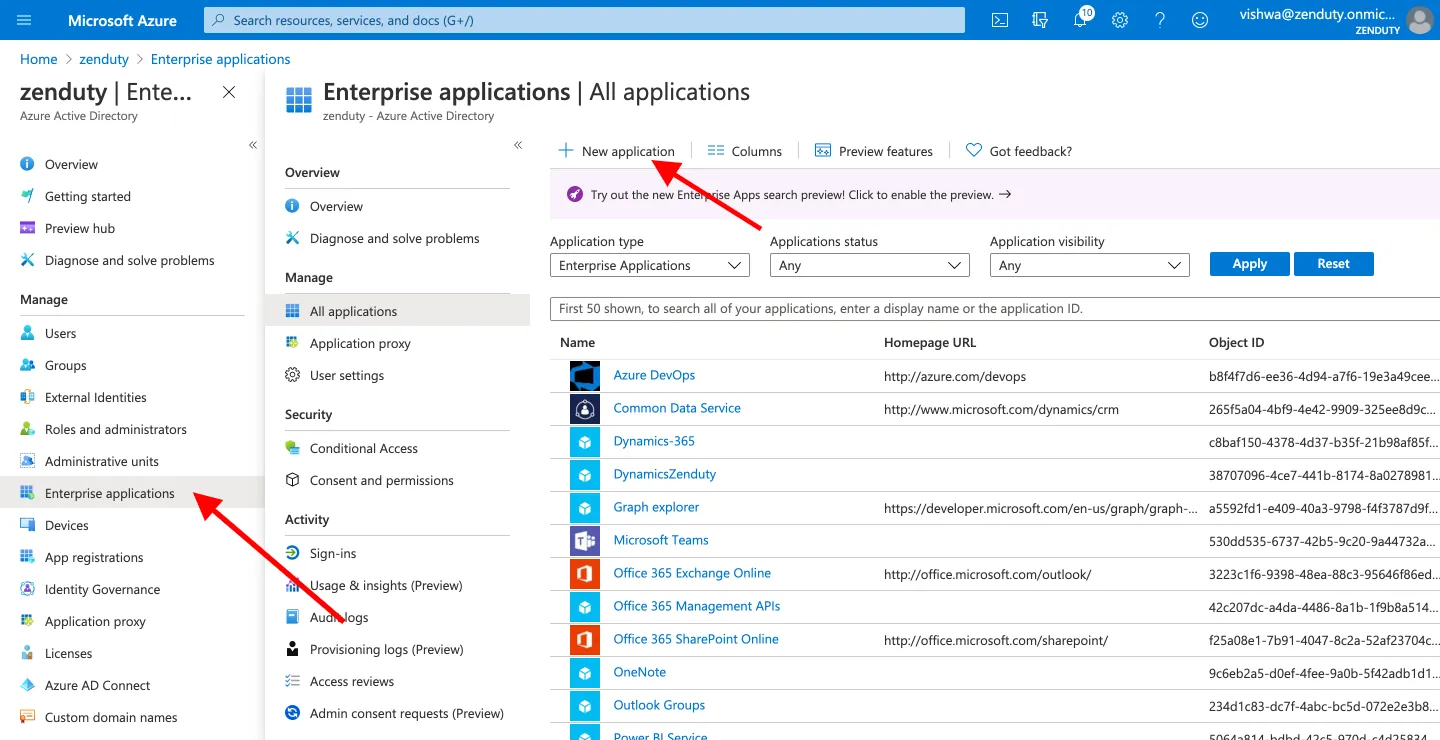
- Go to your Azure portal browser tab. Navigate to Azure Active Directory from the left vertical panel. Navigate to Enterprise Applications from the left vertical panel. Click on New application.
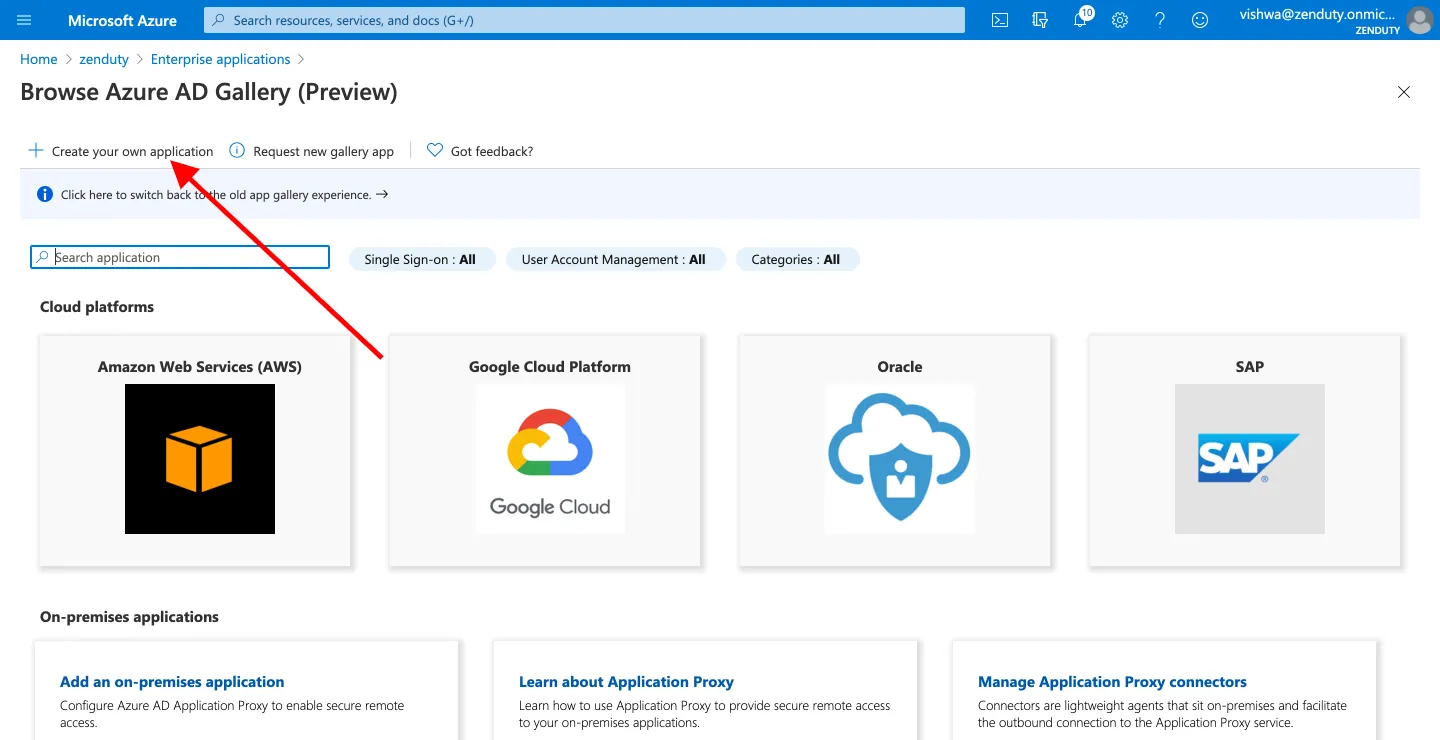
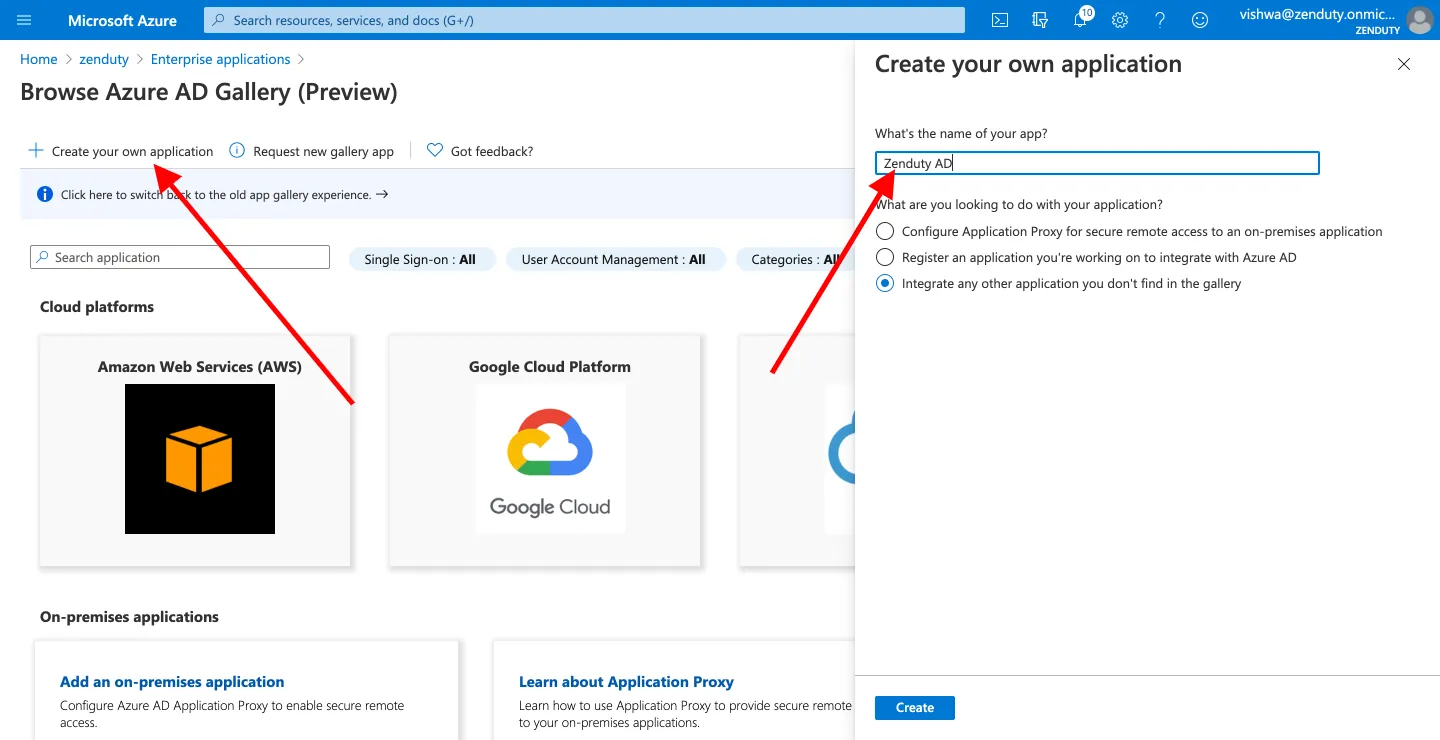
- Click on Create your own application. Name your application as 'Xurrent IMR AD' or any name that you prefer. Select Integrate with any other application you don't find in the gallery from the radio options.
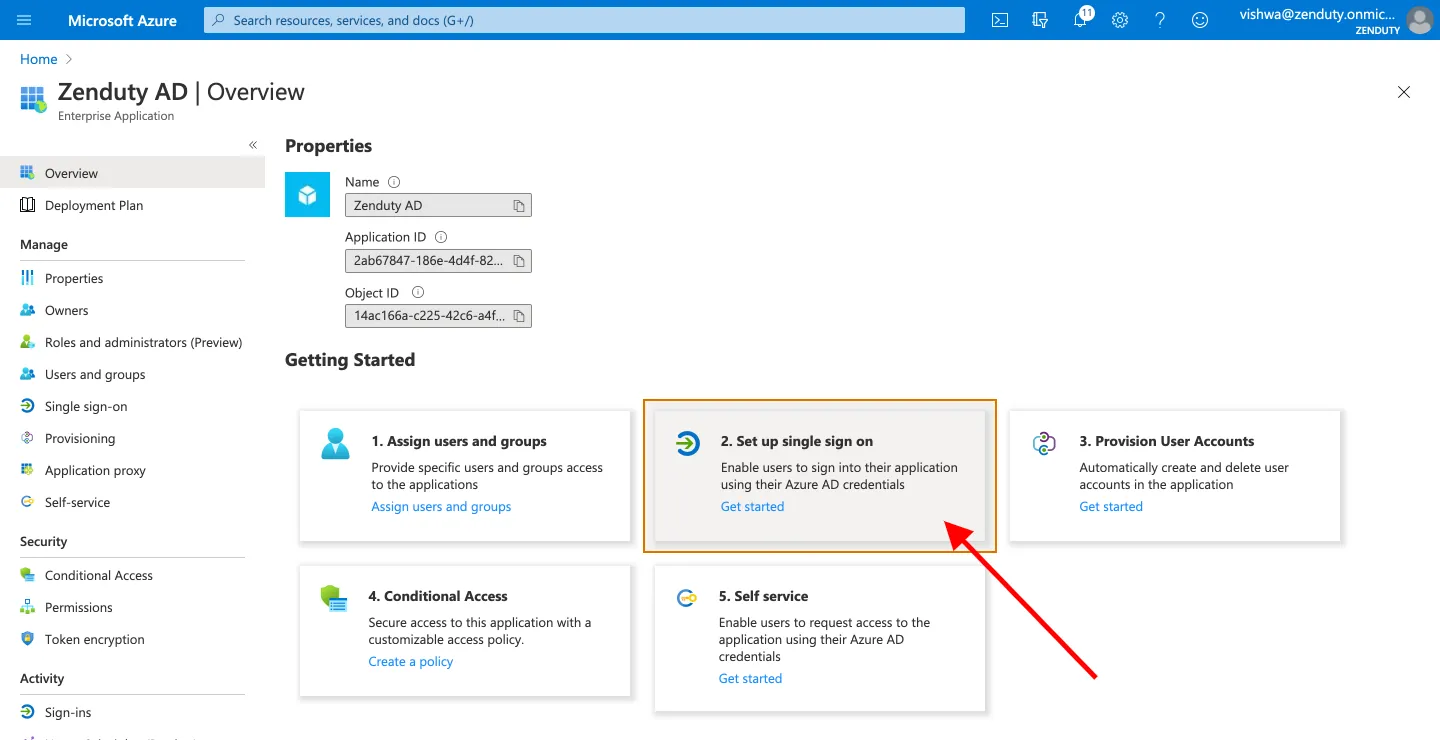
- In the Getting Started area, click on Setup single sign on.
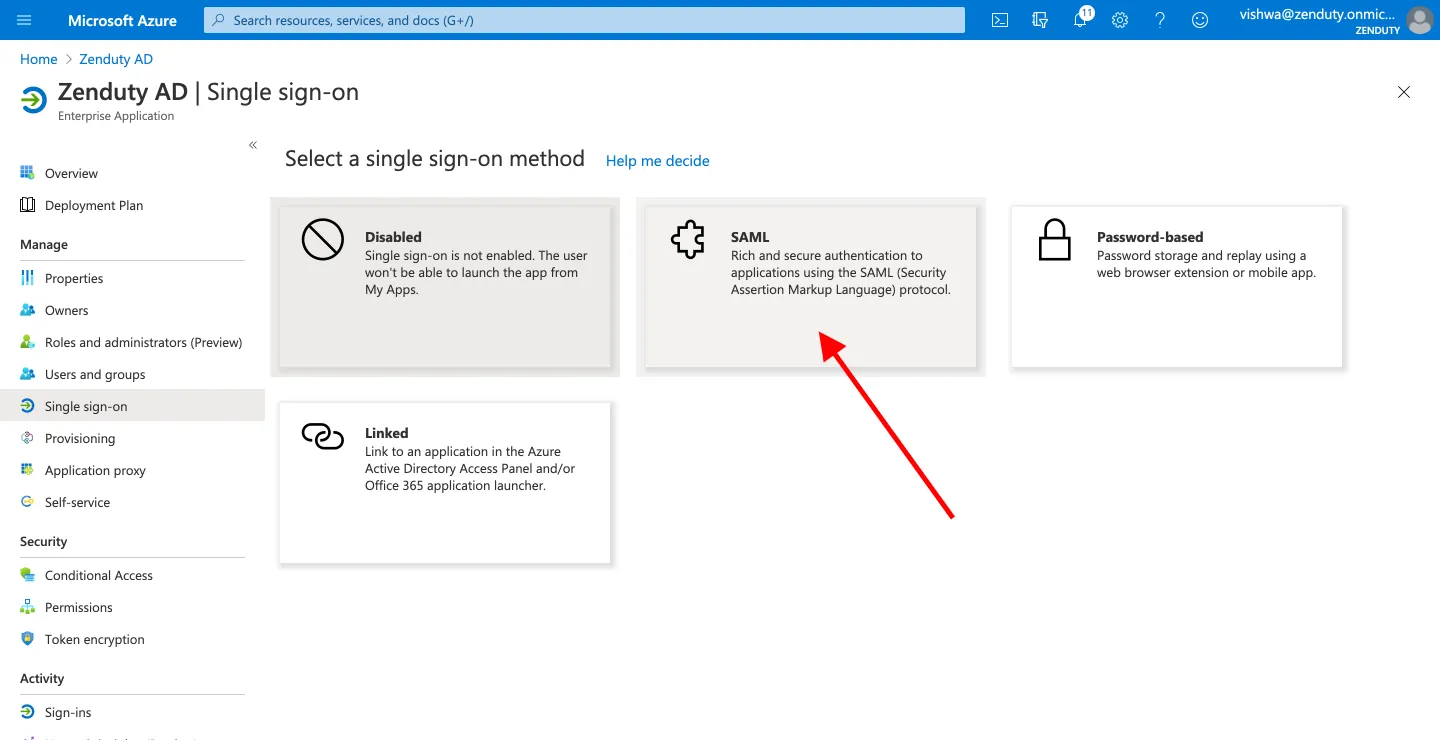
- Click on SAML.
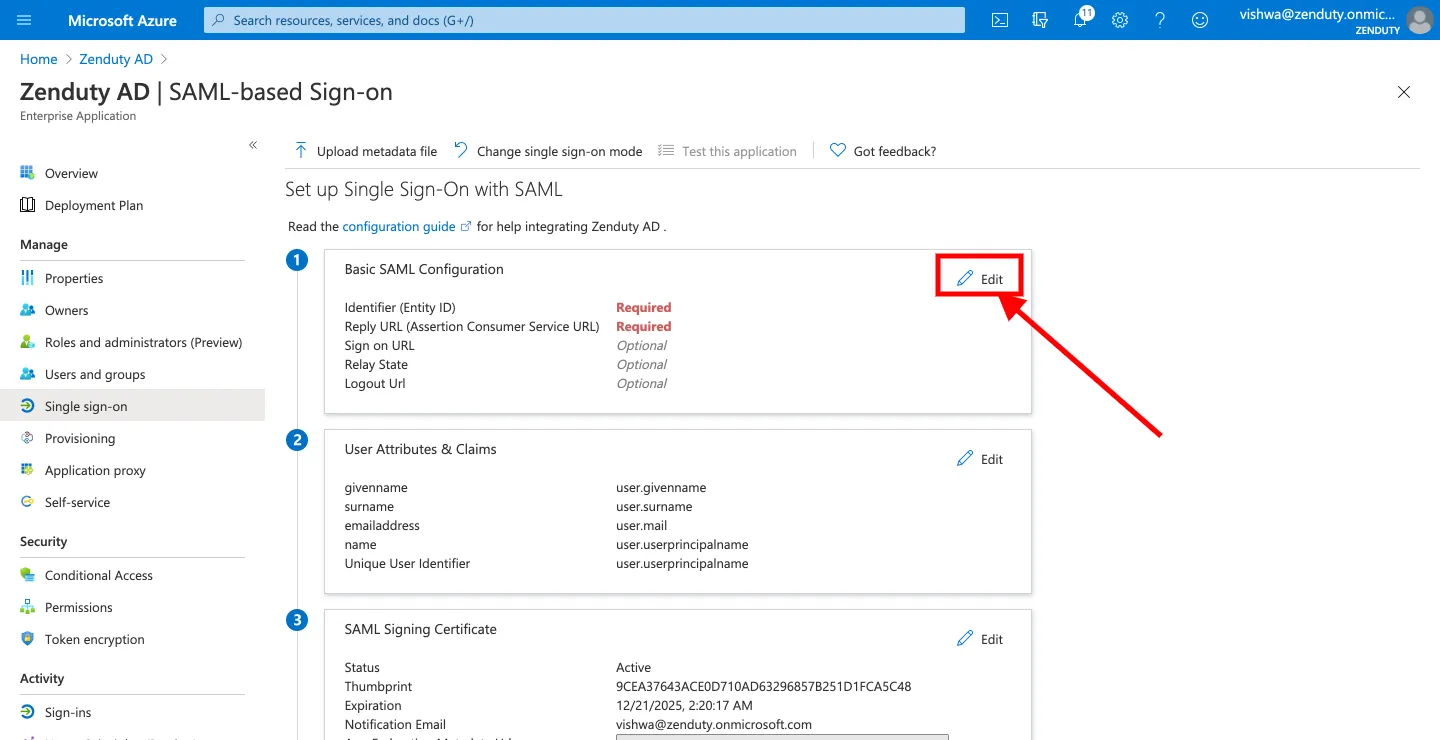
- Click on Edit in the Basic SAML Configuration area.
- In the Identifier(Entity Id) input box, enter the value - https://www.zenduty.com
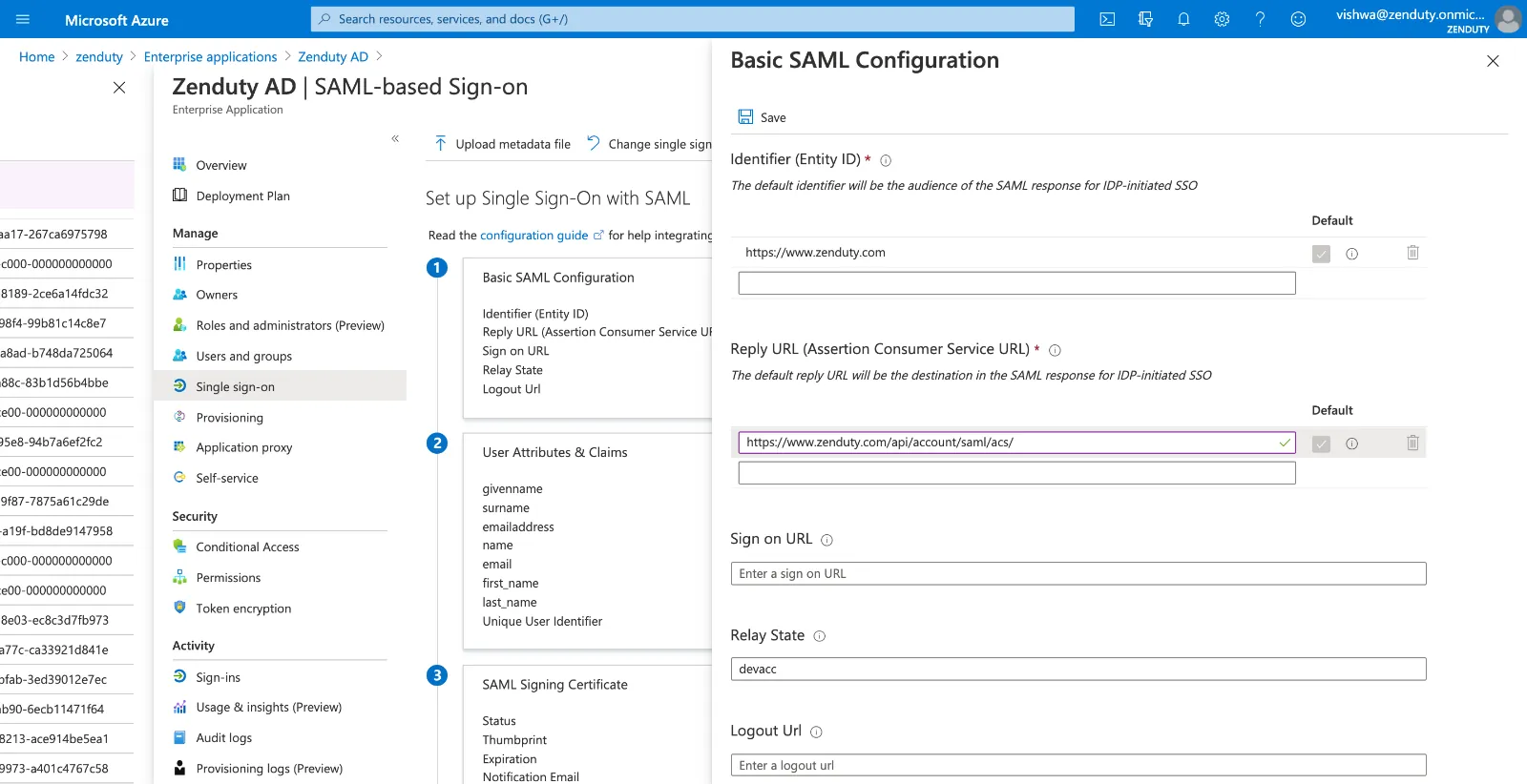
- In the Reply URL(Assertion Consumer Service URL) input box enter the value - https://www.zenduty.com/api/account/saml/acs/
- In the Relay State input box, enter your Xurrent IMR account domain name that you copied in step 2. Click on Save.
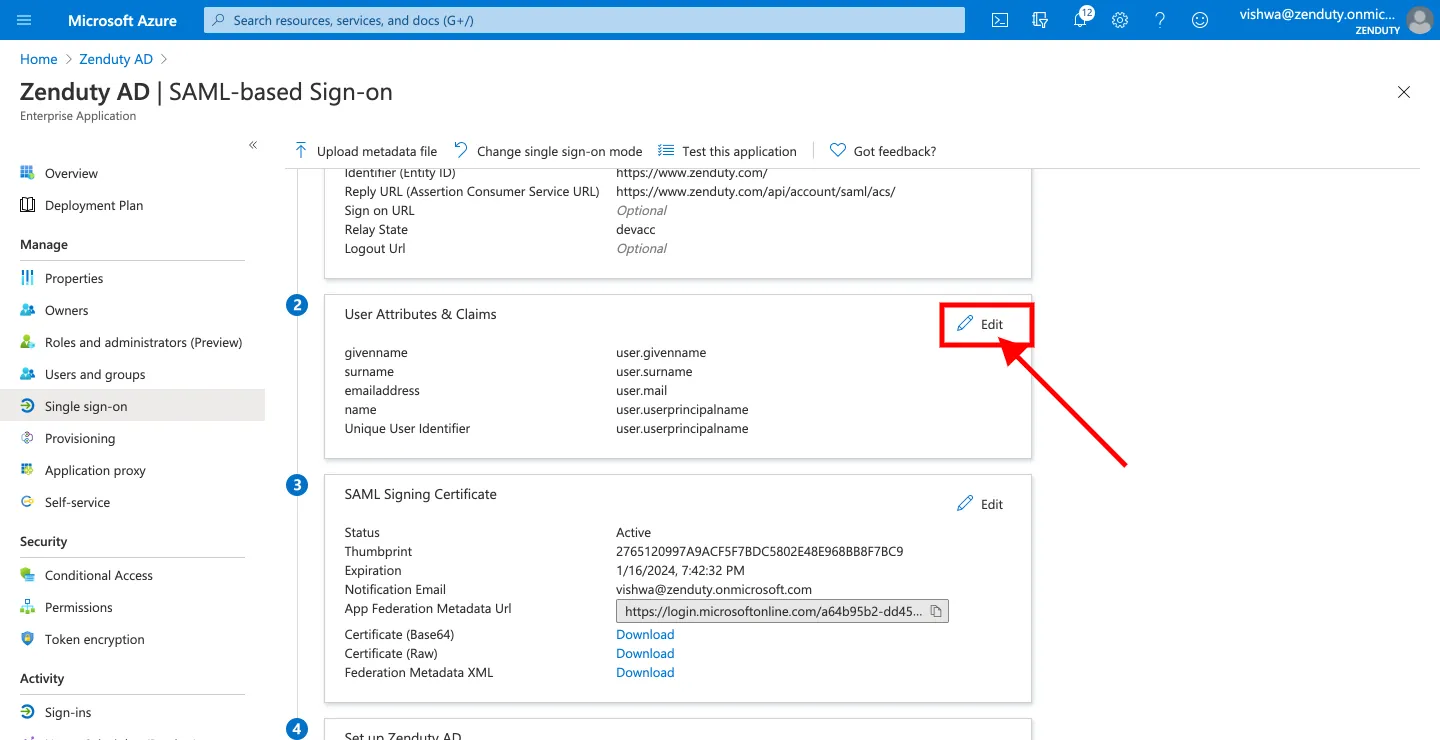
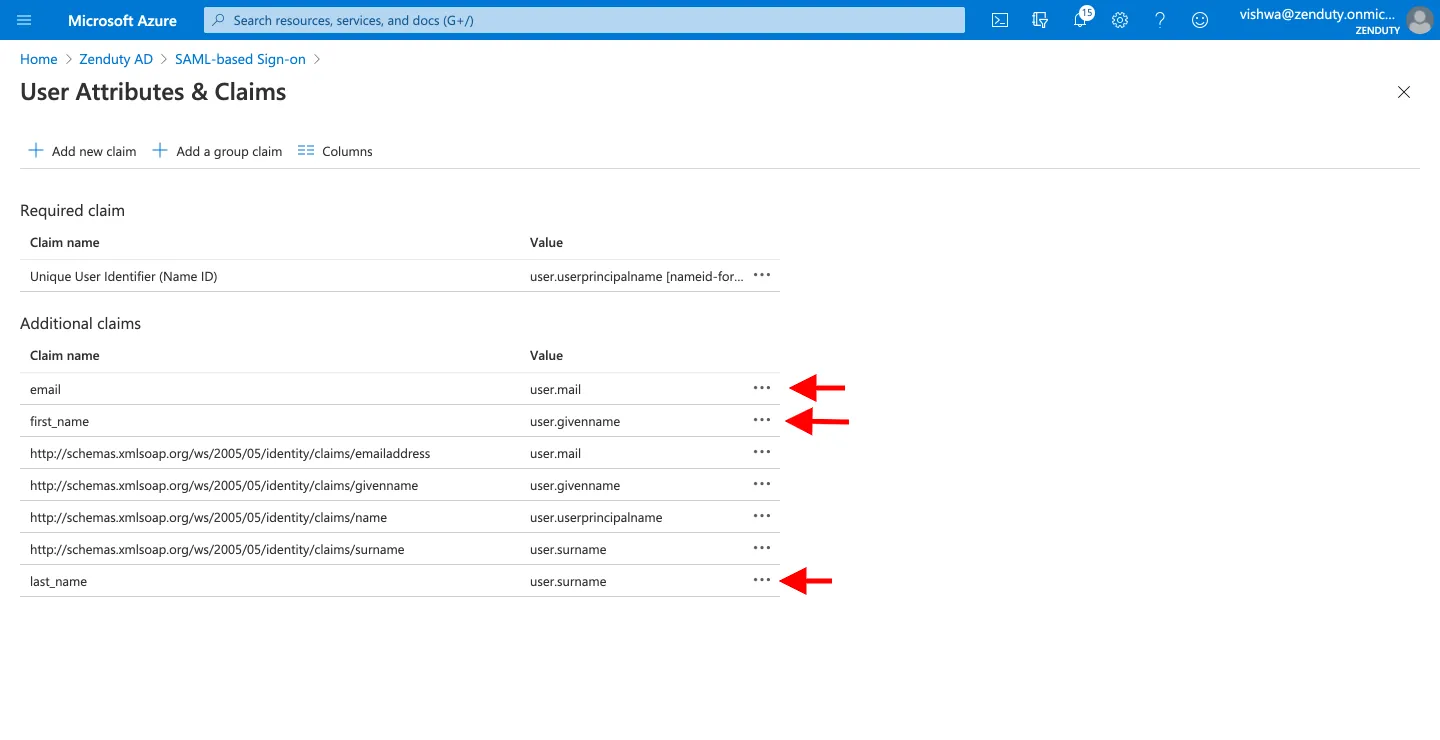
- Click on Edit next to User Attributes & Claims. You need to create three new claims.
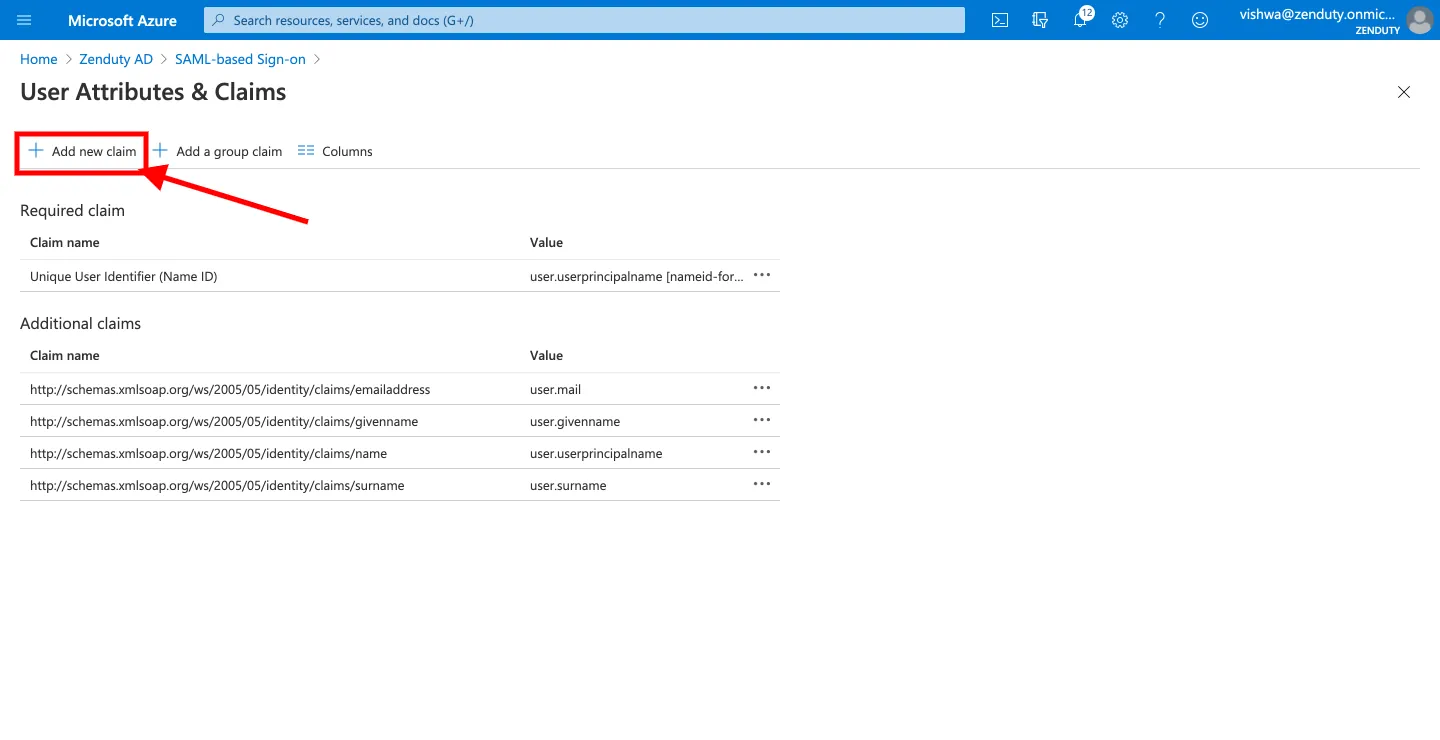
- For the first claim, click on Add new claim(Note: in case the Add new claim button is greyed out, try refreshing your page). In the Name field, enter the value email. In the Source radio options, select Attribute. In the Source Attribute dropdown, search for 'user.mail'.
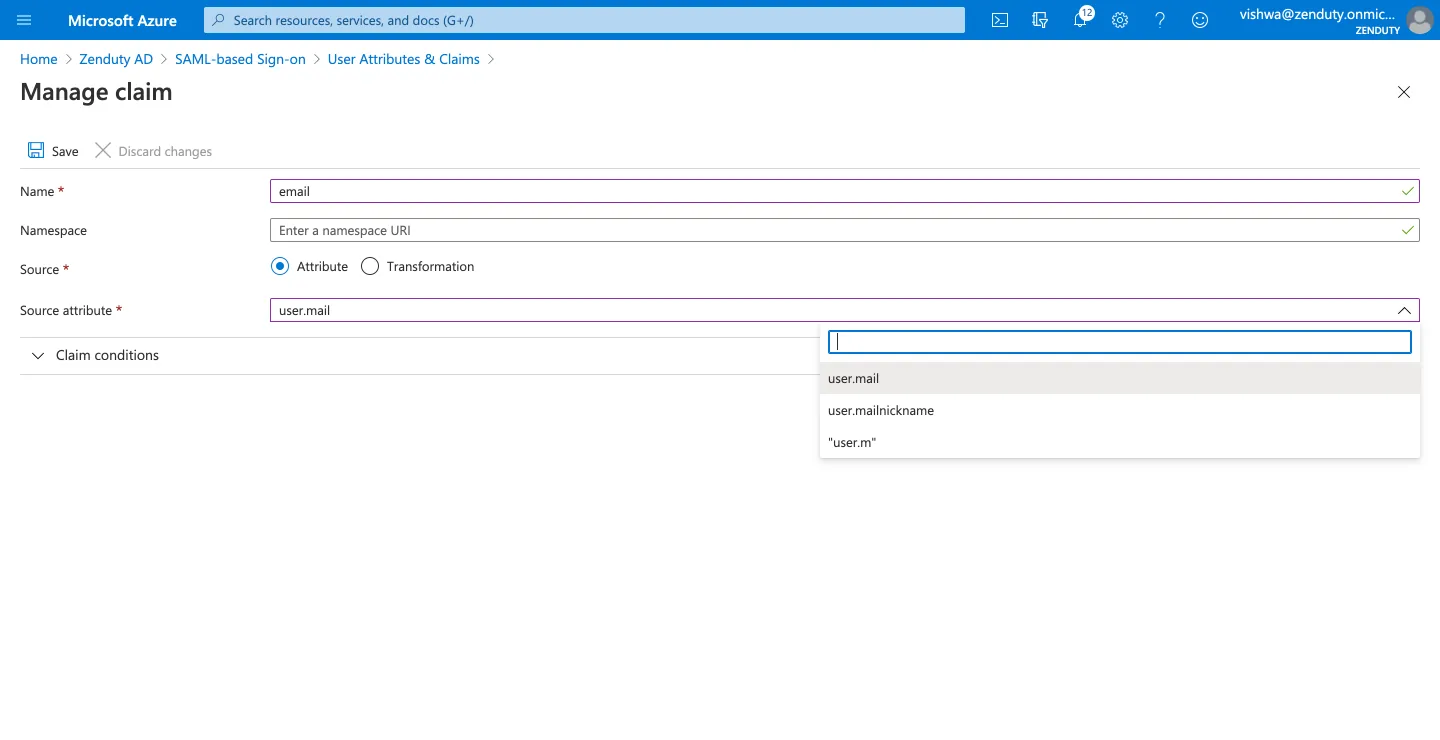
- For the second claim, click on Add new claim. In the Name field, enter the value first_name. In the Source radio options, select Attribute. In the Source Attribute dropdown, search for 'user.givenname'.
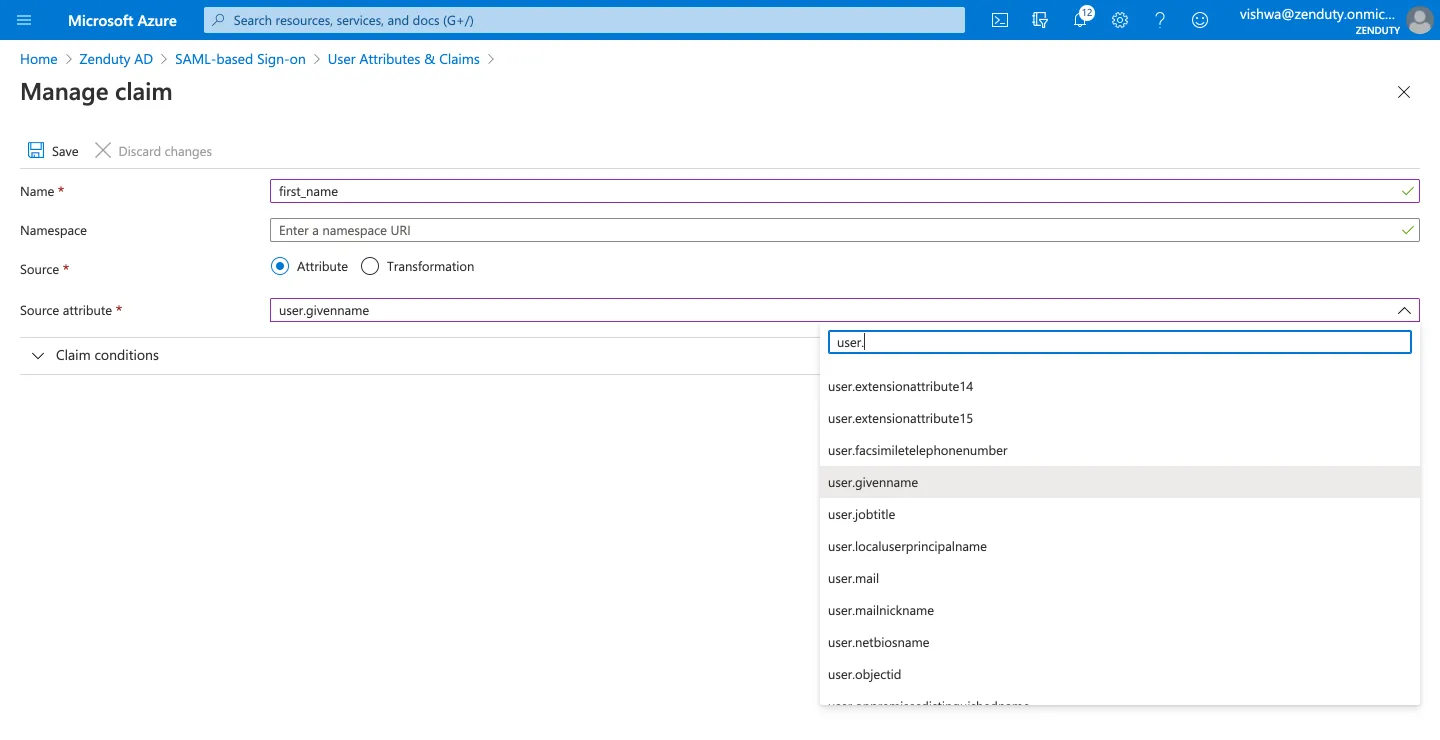
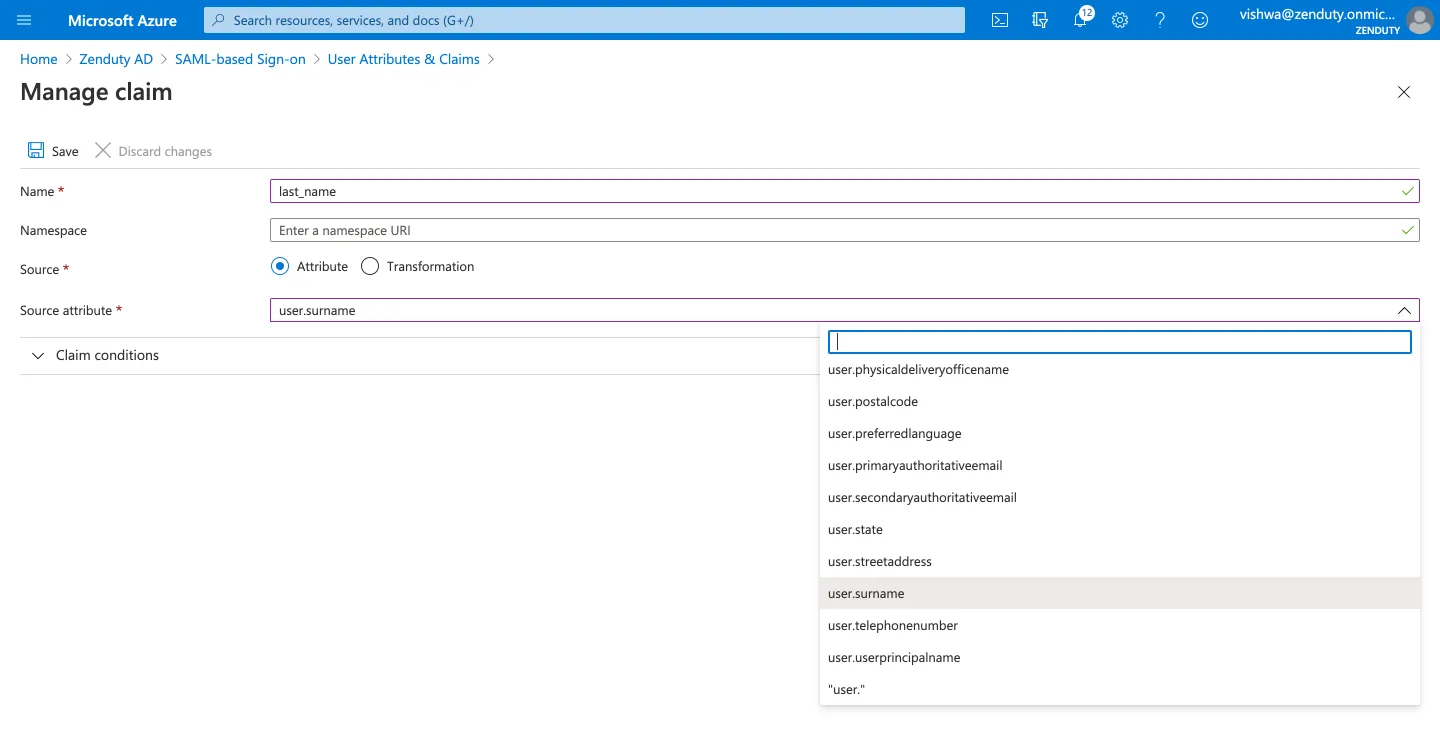
- For the third claim, Click on Add new claim. In the Name field, enter the value last_name. In the Source radio options, select Attribute. In the Source Attribute dropdown, search for 'user.surname'.
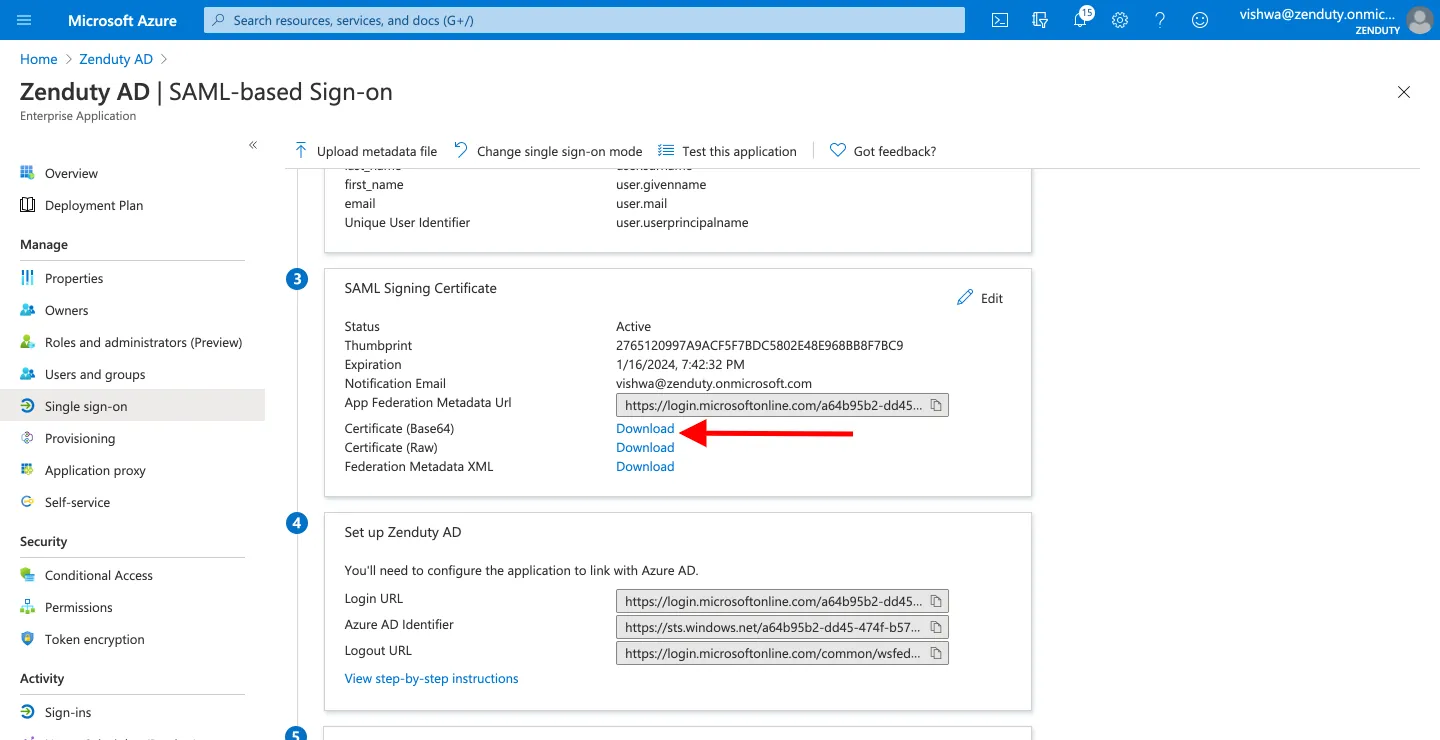
- Navigate back to the Single Sign-on page. In the SAML Signing Certificate area, click on the Download link next to the Certificate (Base64) text. Open the downloaded file.
- Go to the Xurrent IMR tab. Navigate to the Account page from your top right dropdown. Navigate to the Single Sign-on page from the left vertical panel. From the Select SSO Provider dropdown, select Azure Active Directory.
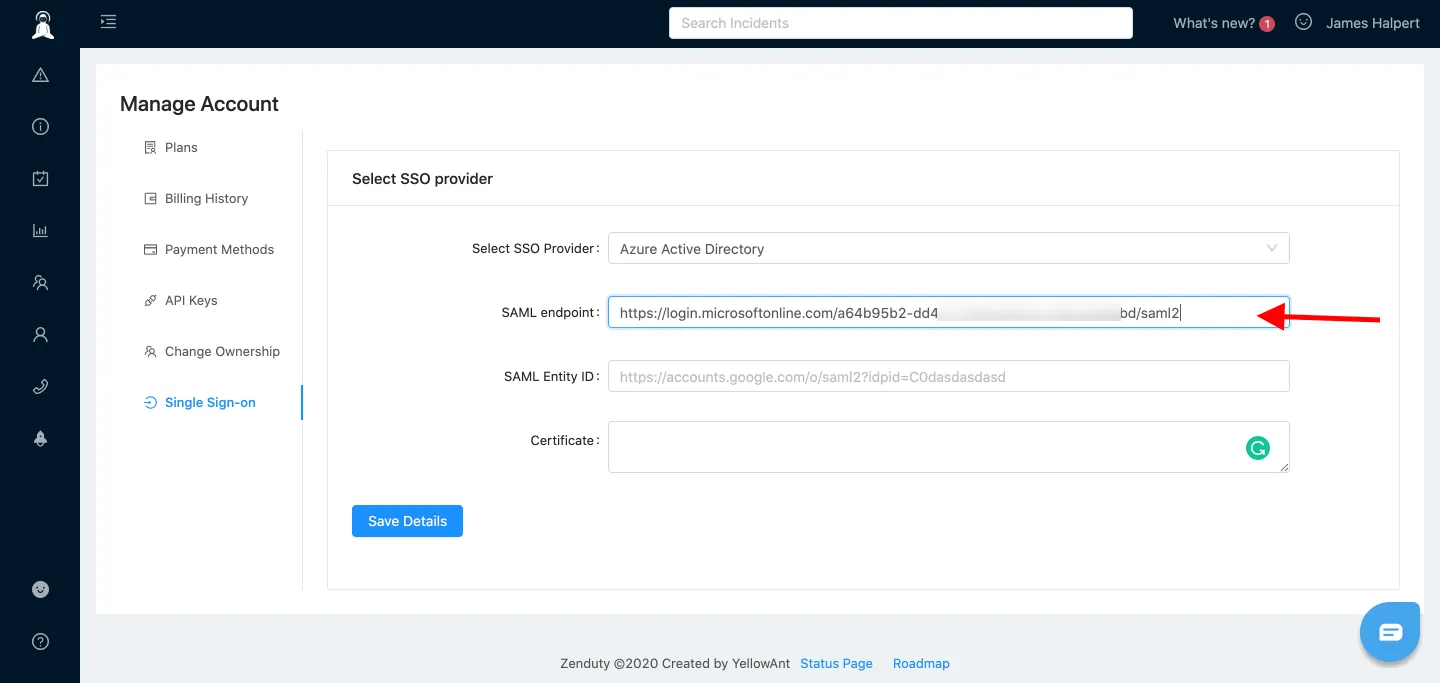
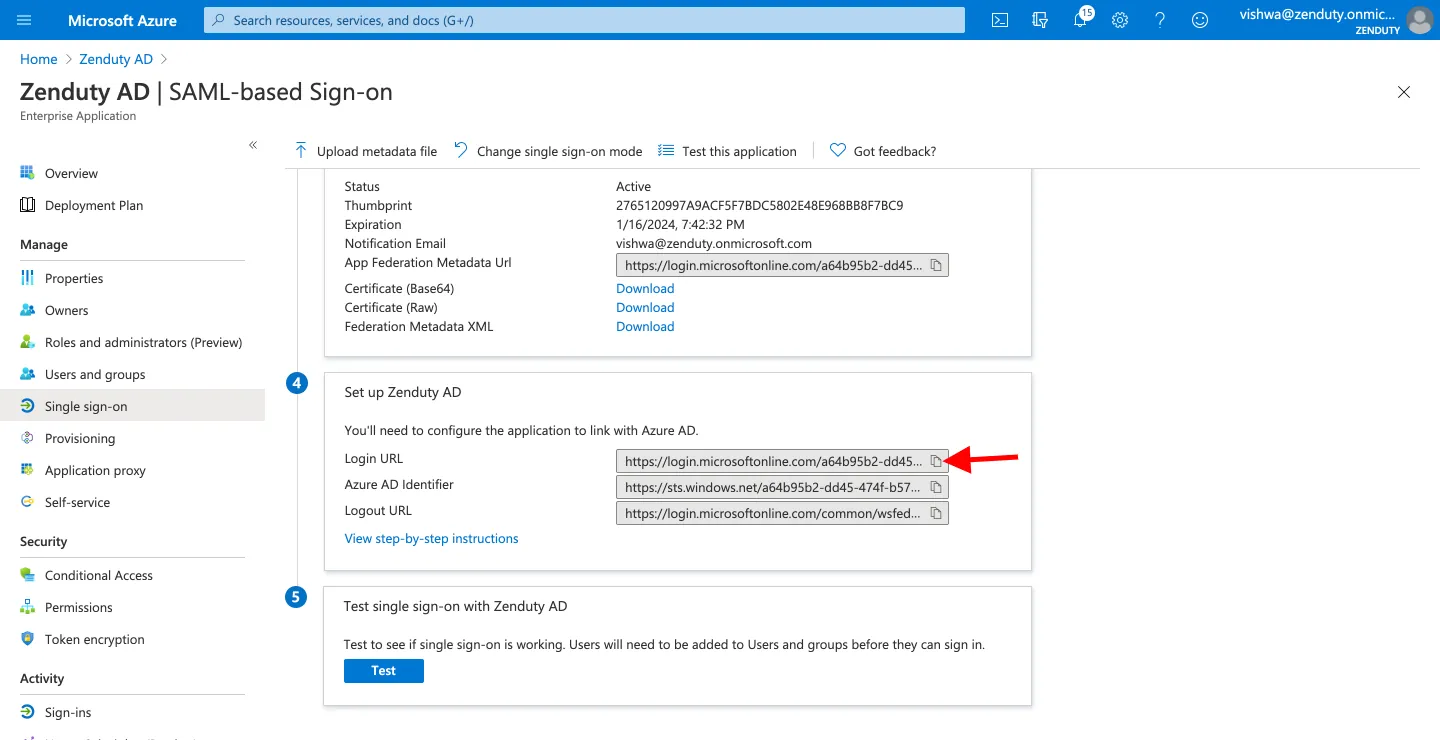
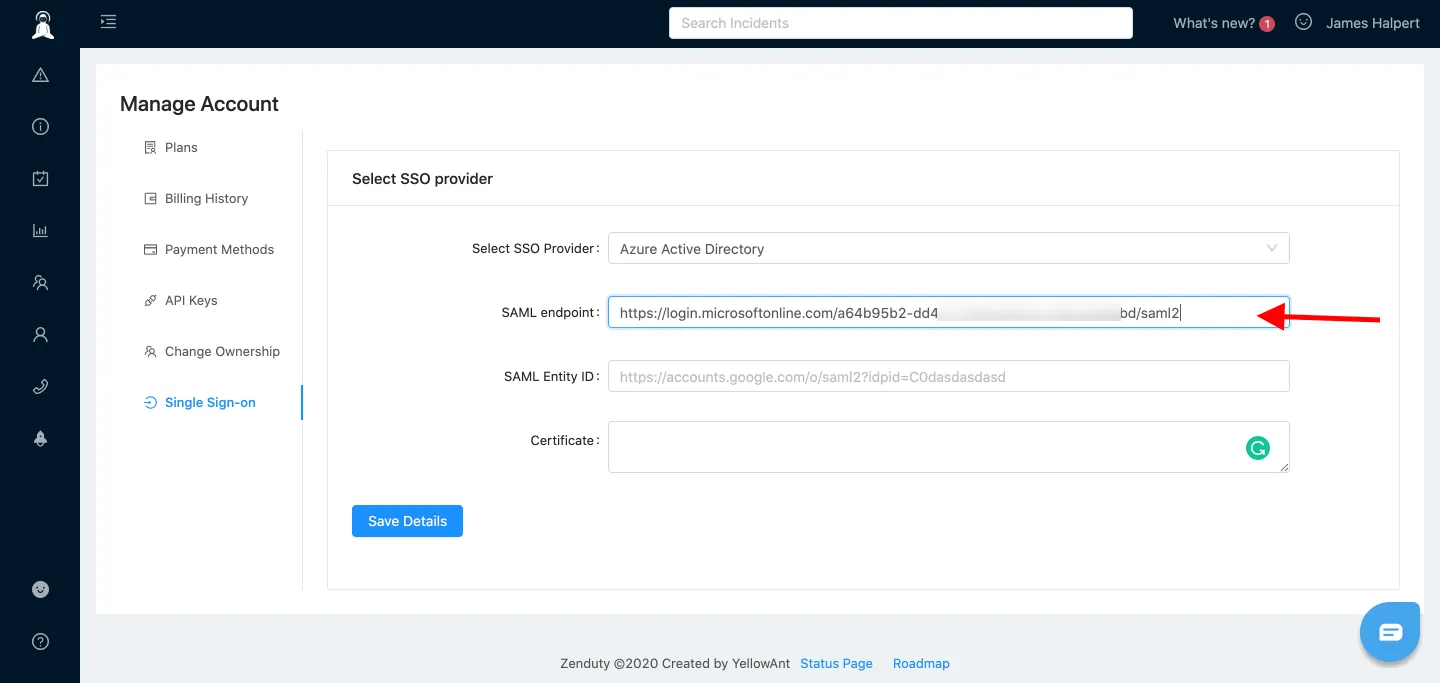
- For the SAML endpoint input box, go back to your Azure tab, and under Set up Xurrent IMR AD copy the Login URL value and paste it into the SAML endpoint input box in the Xurrent IMR tab.
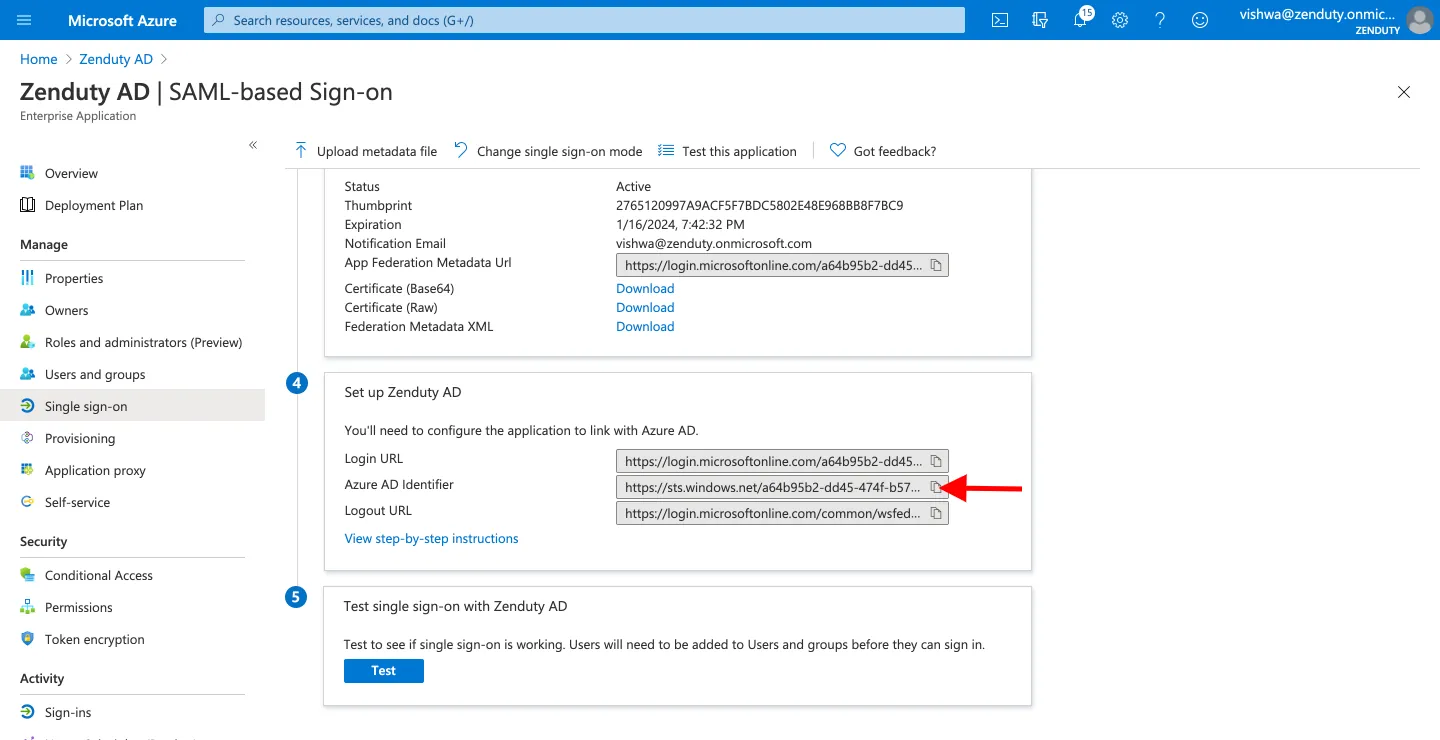
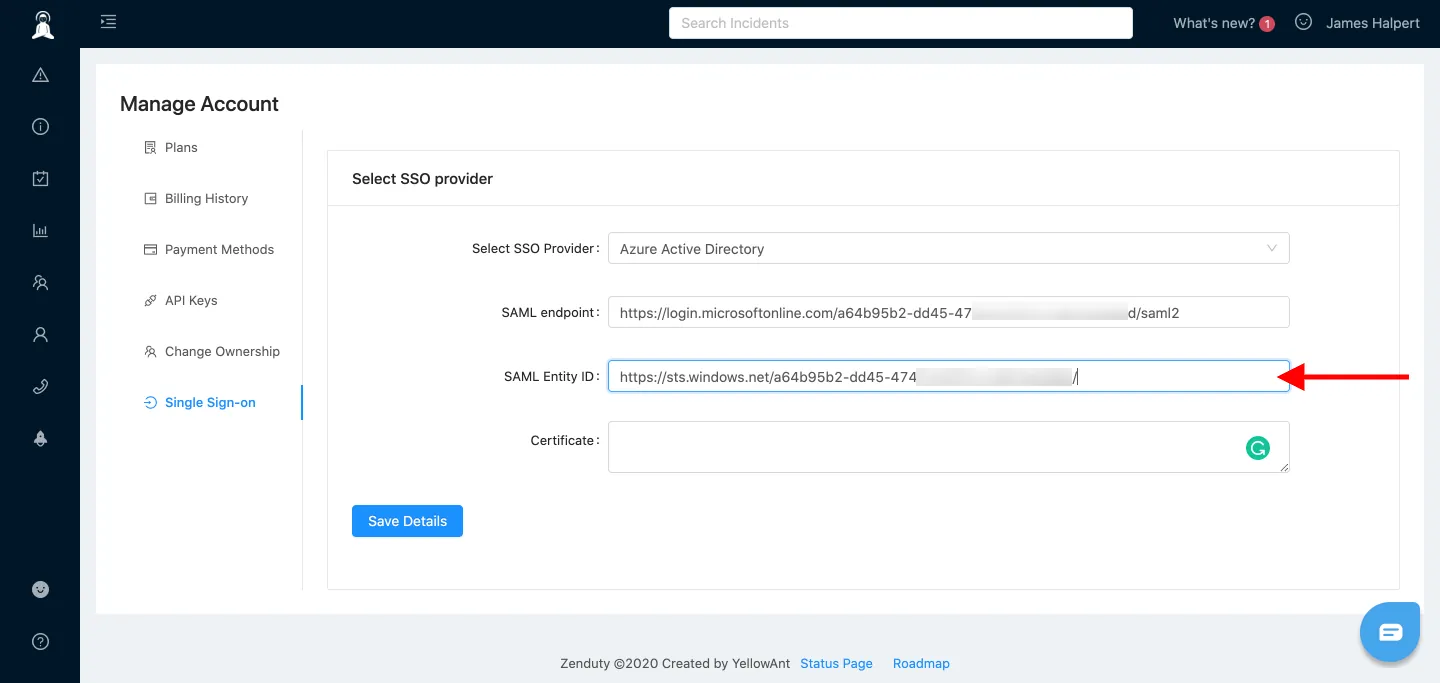
- For the SAML Entity ID input box, go back to your Azure tab, and under Set up Xurrent IMR AD copy the Azure AD Identifier value and paste it into the AML Entity ID input box in the Xurrent IMR tab
- For the Certificate input box, open the Base64 certificate downloaded in Step 15 in a text file, copy the certificate text and paste into the Certificate input box.
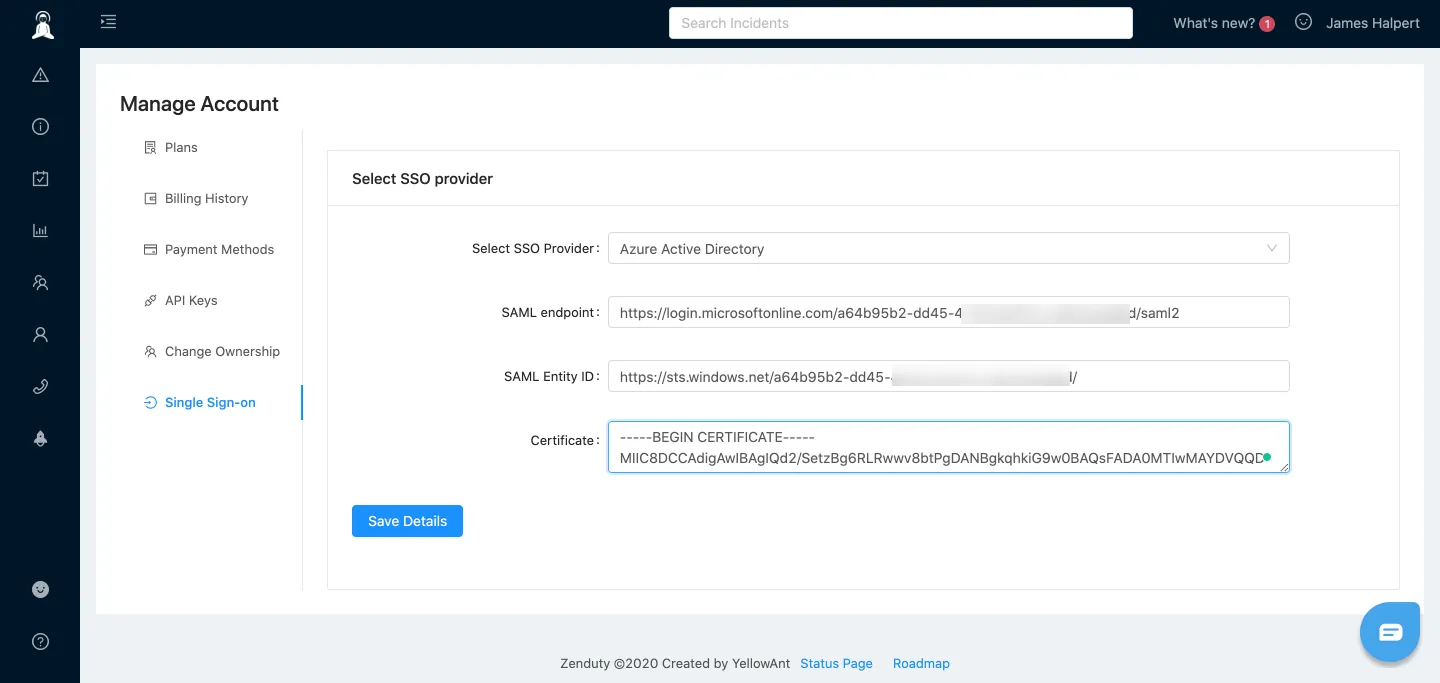
- Click on Save Details.
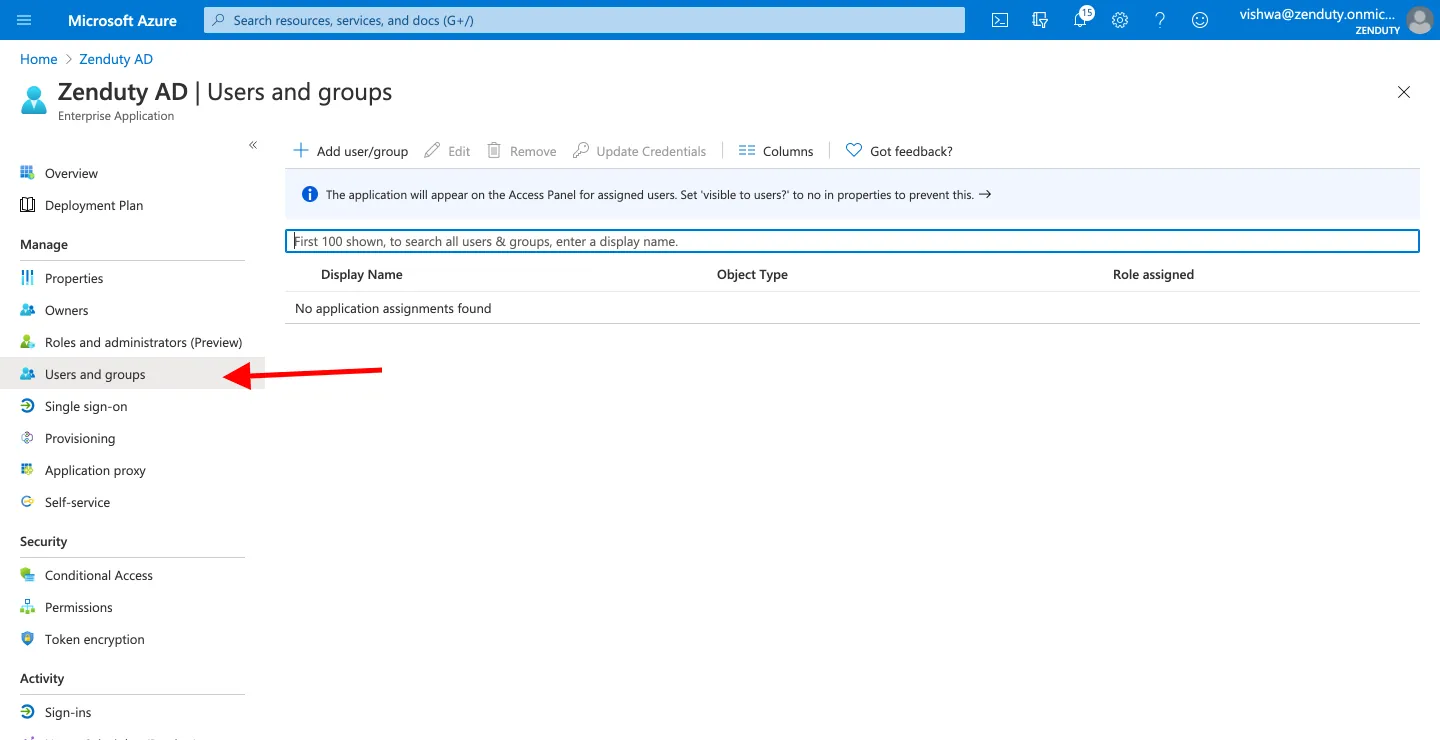
- Navigate back to your Azure Single Sign on tab. Click on Users and groups on the left vertical navigation panel. Click on Add user/group. Add the users you want to provide access to Xurrent IMR.
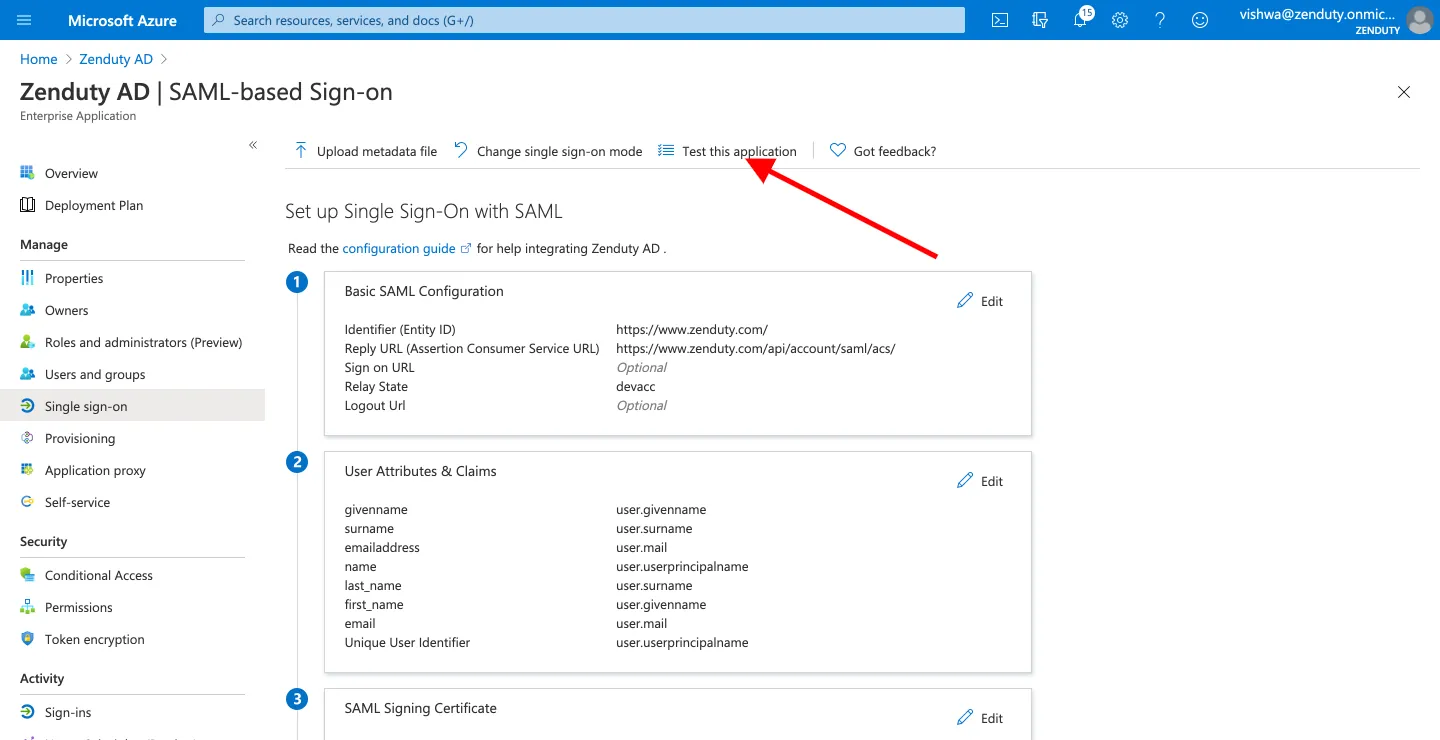
- To test the setup, logout from Xurrent IMR. Go back to the Single Sign-on page from the left vertical navigation panel in your Azure AD tab. Click on Test this application; on the top. Click on Sign in as current user. Authenticate your Azure account. You should be redirected to your Xurrent IMR page.
- For the final test, logout of Xurrent IMR. In your browser, navigate to the Xurrent IMR Login Page. Click on Log in with your Identity Provider. In the domain input box, enter your account domain name(copied from Step 2). Click on continue. You will be redirected to your Azure AD login. Authenticate your Azure account. You will be redirected to your Xurrent IMR dashboard.
Your Azure AD integration is complete!
Disable password login for non-admin users
To disable password login for non-admin users, you can toggle the "Allow Email and Password login for users" setting in the SSO configuration

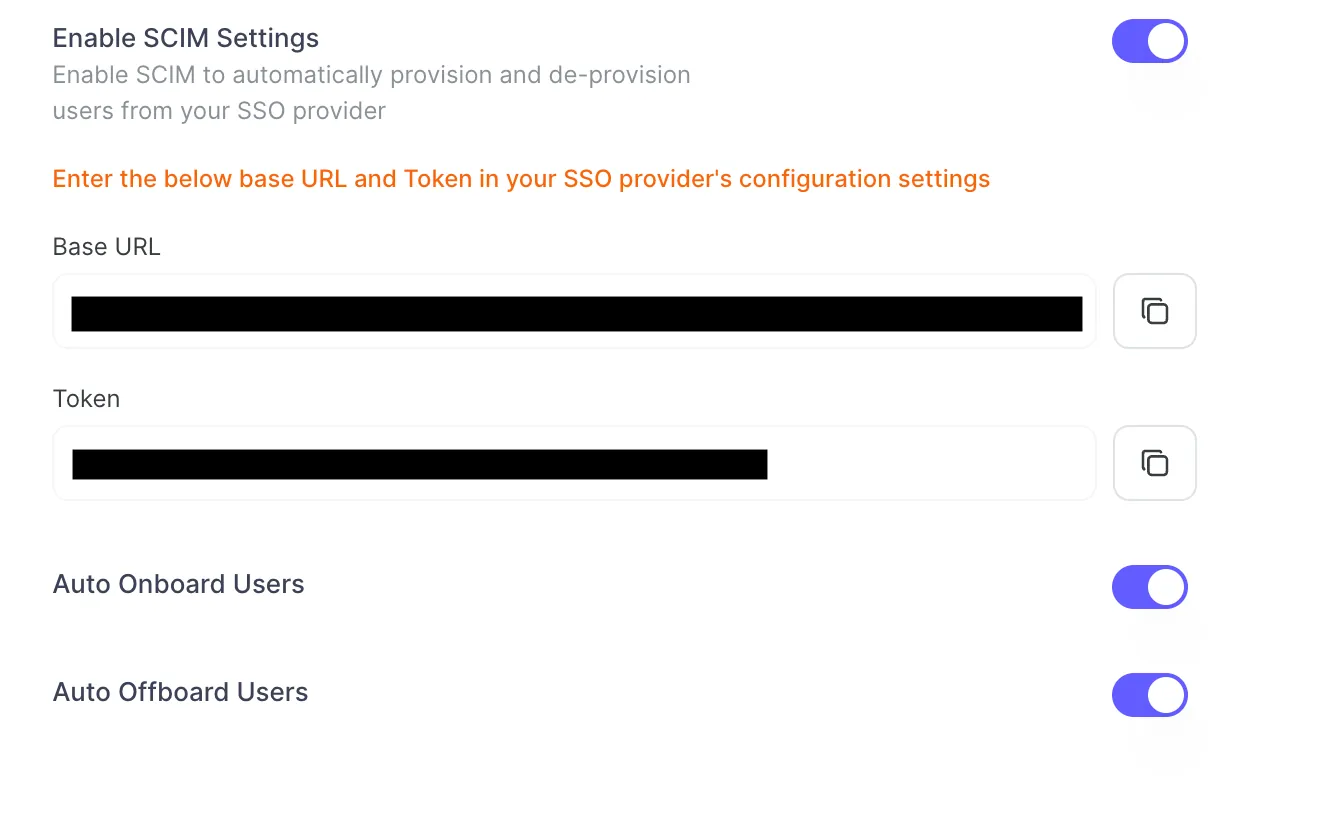
Enable SCIM Settings in Xurrent IMR
- Toggle the Enable SCIM Settings to activate user provisioning.

- Copy the Base URL and Token provided. Save them securely — you’ll need these for Azure AD configuration.
- Go to Xurrent IMR AD application in Azure AD portal.
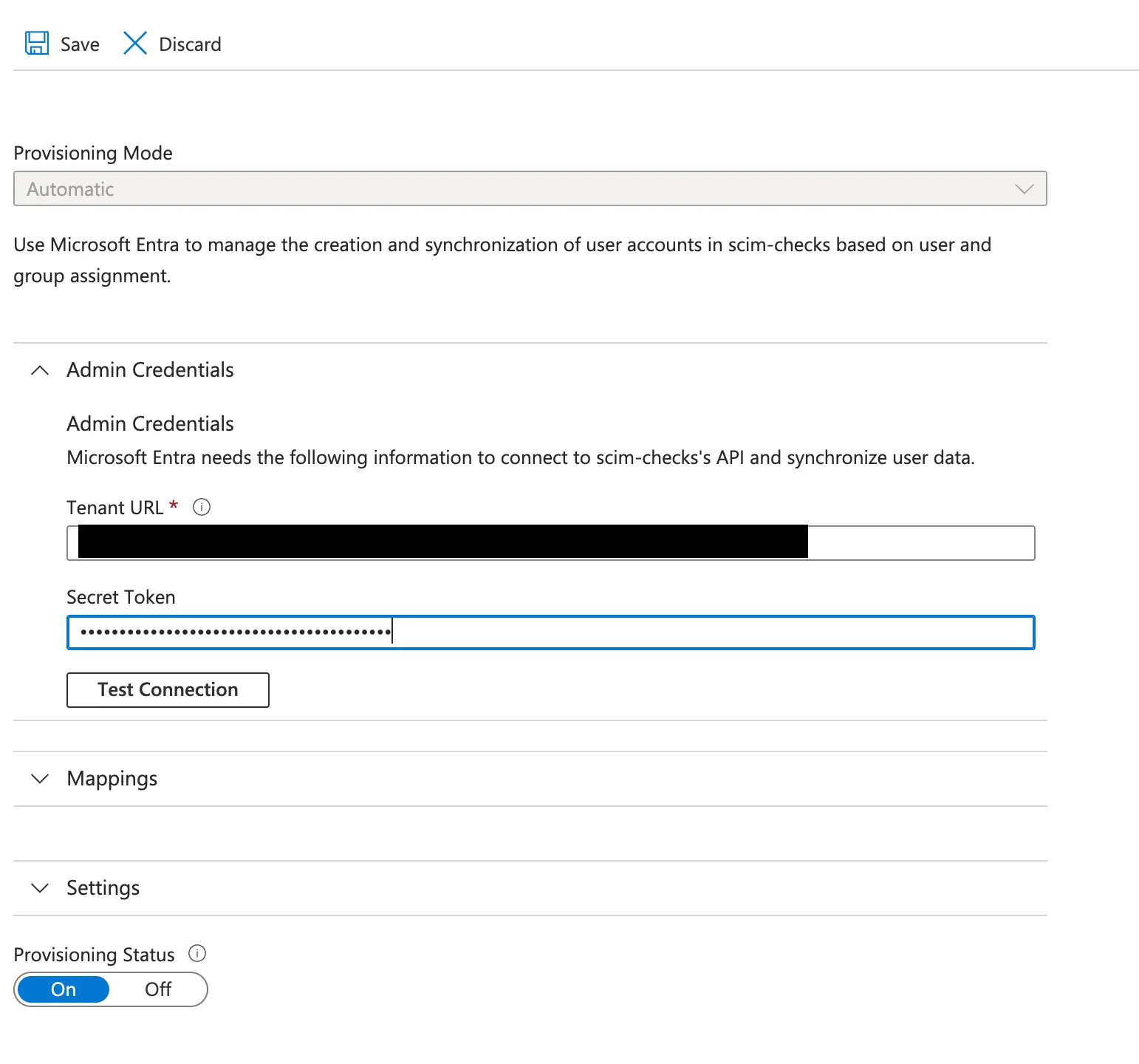
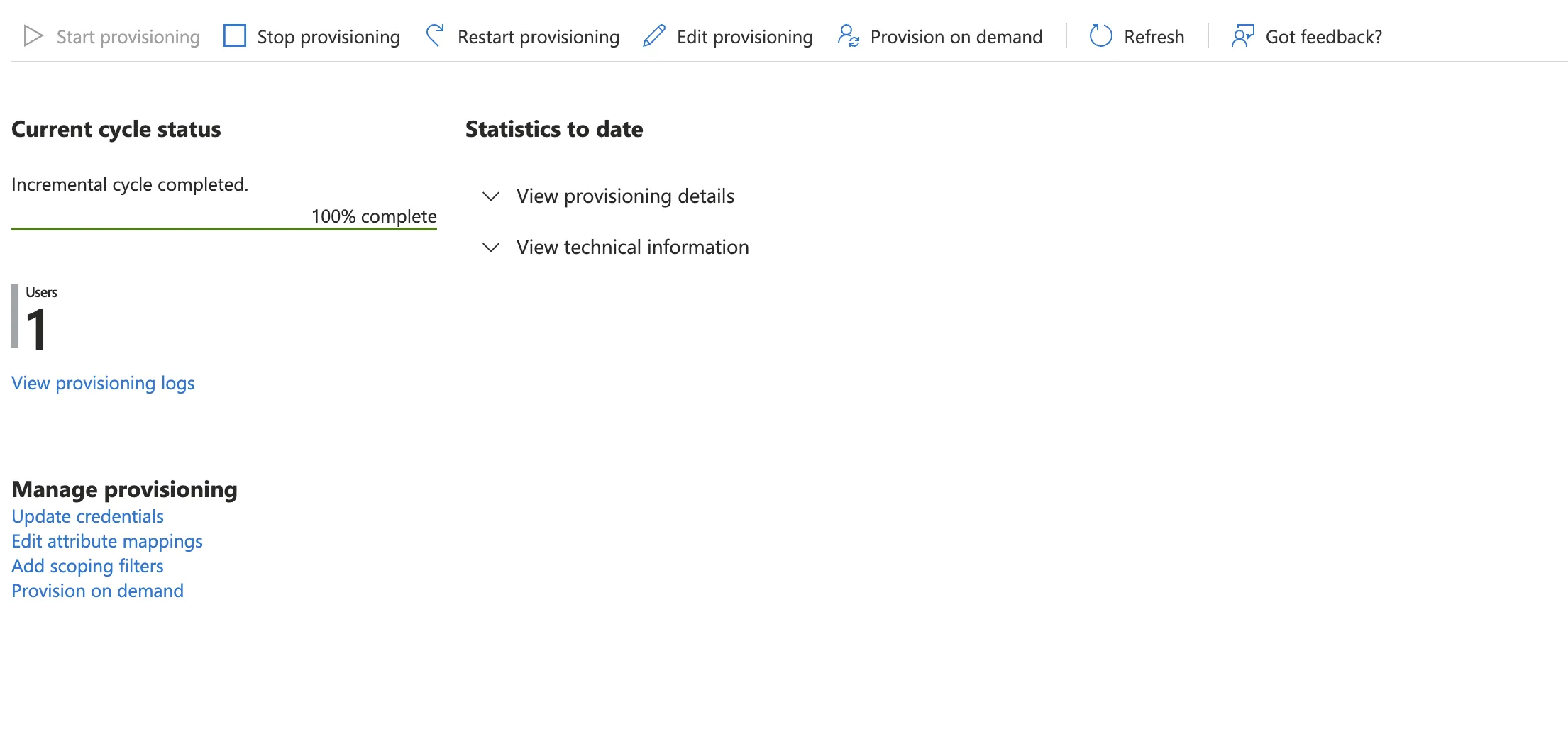
In the Manage section, click on Provisioning. Under Provisioning Mode, select Automatic, in the Admin Credentials section, Paste the Base URL and Token you copied from Xurrent IMR then, Click Test Connection to verify the credentials.
- Under the Mappings section, click on Provision Microsoft Entra ID Users.
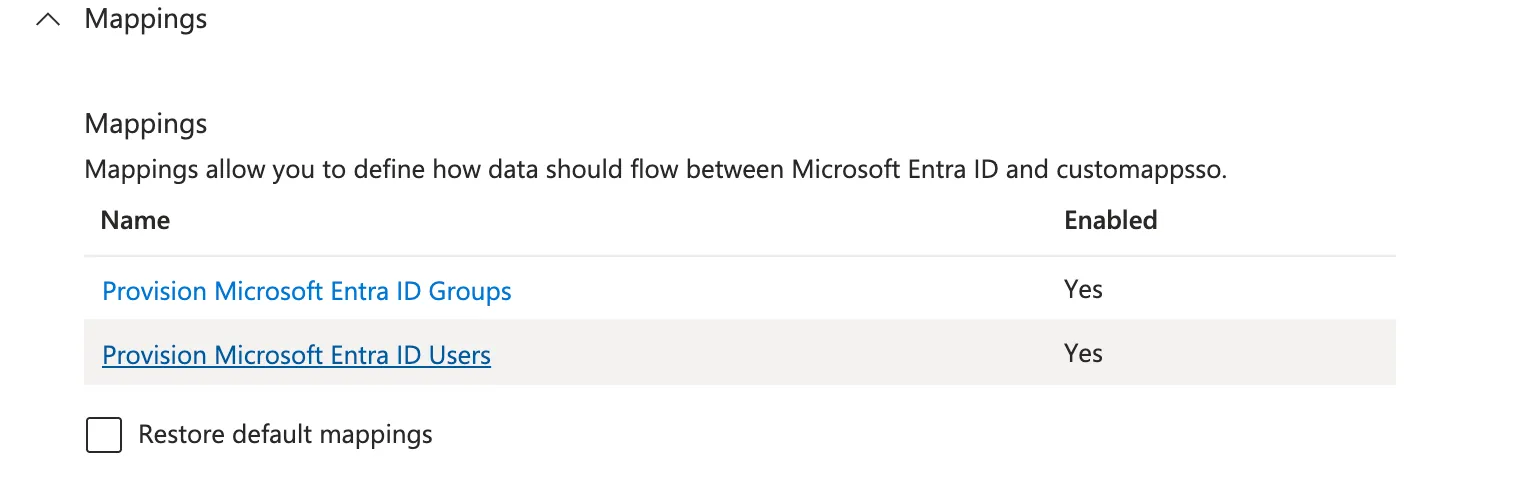
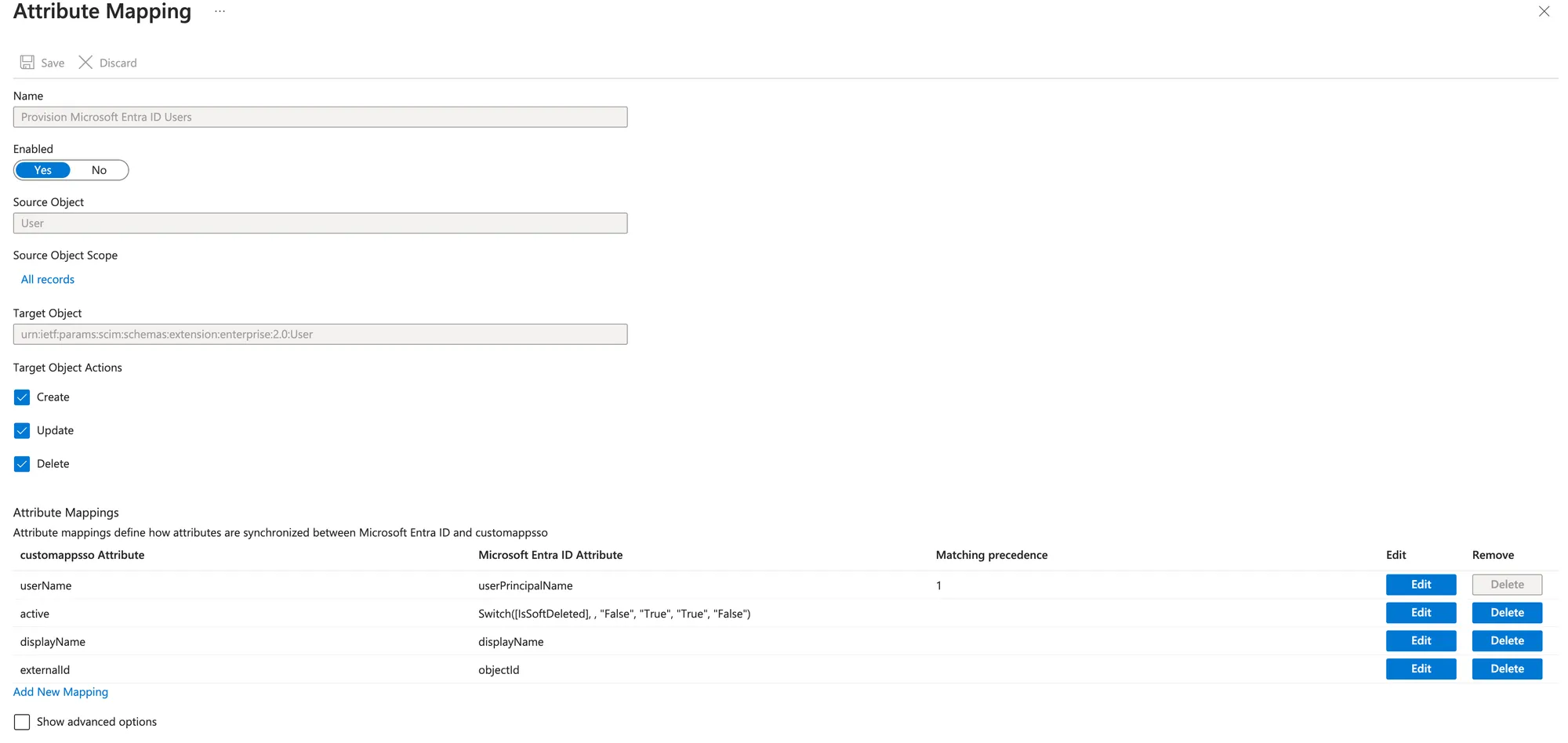
- Toggle Enabled to Yes, Ensure Create, Update, and Delete actions are selected and map the user attributes as shown below and save the Attribute Mapping.
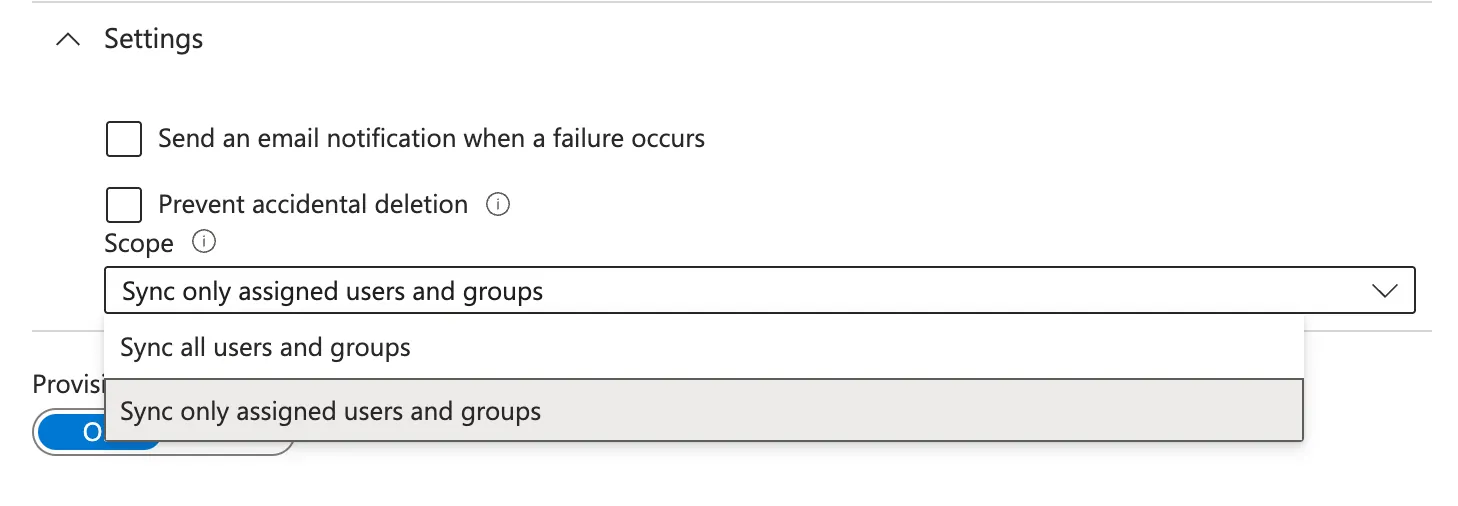
- In Provisioning configuration under the Settings section, From the Scope dropdown, select Sync only assigned users and groups. Toggle the Provisioning Status to On then click Save.
- Navigate to the Users and Groups section under Manage. Add and assign all users you wish to provision to Xurrent IMR via this application then Go to the Overview section of the Xurrent IMR AD application and Click Start Provisioning to begin syncing users.
Important! Auto Deprovisioning Note:
To automatically delete a user from Xurrent IMR, unassign the user from the Xurrent IMR AD application. Do not delete the user directly from Azure Active Directory — this will not trigger the deprovisioning action in Xurrent IMR.
You have successfully set up SCIM-based user provisioning between Azure AD and Xurrent IMR.












.webp)
%20(1).webp)
.jpg)

.jpg)