Insights & updates from our experts
Xurrent IMR's Role Based Access Control
Role Based Access Control is a feature set available for growth and enterprise users providing fine-grained access management of Xurrent IMR. Xurrent IMR RBAC allows you segregate duties and access within your team and grant only the permissions to users that they need to perform their responsibilities.
If RBAC is not enabled, Xurrent IMR's default role structure follows with the pre-defined roles of Owner, Admin, Team Manager and User.
What can I do with RBAC?
- Create custom account roles with specific permissions and assign it to groups of users with similar responsibilities and use cases. For eg: customized roles for Engineering Managers could have
viewpermissions for all teams, allowing for visibility into the entire organization. - Change a team's settings to grant all users certain specific permissions. For eg: the Database team's incidents can be configured to be viewable by all dependant users allowing them to correlate Database issues with other incidents.
- Enable incident responders to pull in other associated team's on-call users, allowing for more effective collaborative triaging and a decrease in fire-fighting friction.
An organisation can implement RBAC via 2 mediums:
- Team Level Permissions i.e. making some data associated to a team to be visible to non-team members across your Xurrent IMR account
- Account Level Permissions i.e. making custom roles and assigning to users granting them certain chosen permissions only
Team Level Permissions
By default, only the members of a team can view the incidents, escalation policies, schedules, services and other associated information. However, users can harness this ability to tinker with the privacy permissions of a team and make some or all data attached to the team visible to all non-team members of your Xurrent IMR account. This allows for the operational status of teams that are centerpieces of an organisation's engineering structure be accessible to all dependant members.
The final permission set of a user is a union of their account level permissions and a particular team's permissions, implying that even if a user with a custom role is denied permission to view incidents in general, they'll be able to access incidents of a particular team that has configured their incidents to be visible to all members in their team level permissions.
Modifying Team Level Permissions
Only the Account Owner, Account Admins and Team Manager can modify team level permissions.
- Click on the team whose permissions you'd like to edit from the Teams section, navigate to the Settings tab on the very bottom.
- Switch the Access Level setting from Private to Restricted.
- Select the restricted permissions that you'd like to provide to non-team members and click on Update.

List of Team Level Permissions
Note: Selecting some permissions would automatically select others that the chosen permission requires.
Account Level Permissions
Via account level permissions, users can create custom roles and assign to users to grant them specific access to Xurrent IMR resources. This allows organisations to grant special privileges to certain power users and owners, thus lowering dependencies on other responders in dire situations and smoothening the incident resolution process.
Modifying Account Level Permissions
Only the Account Owner and Account Admins can create custom roles and assign them to users.
- Click on your profile bubble on the top-right corner and then on Account.
- Navigate to the Custom Roles section, and click on the Add New Role button.
- Fill in the Name and Description fields, select the permissions as desired. For eg: we create a custom role for Engineering Managers that can view all teams and associated data. Click on Create.
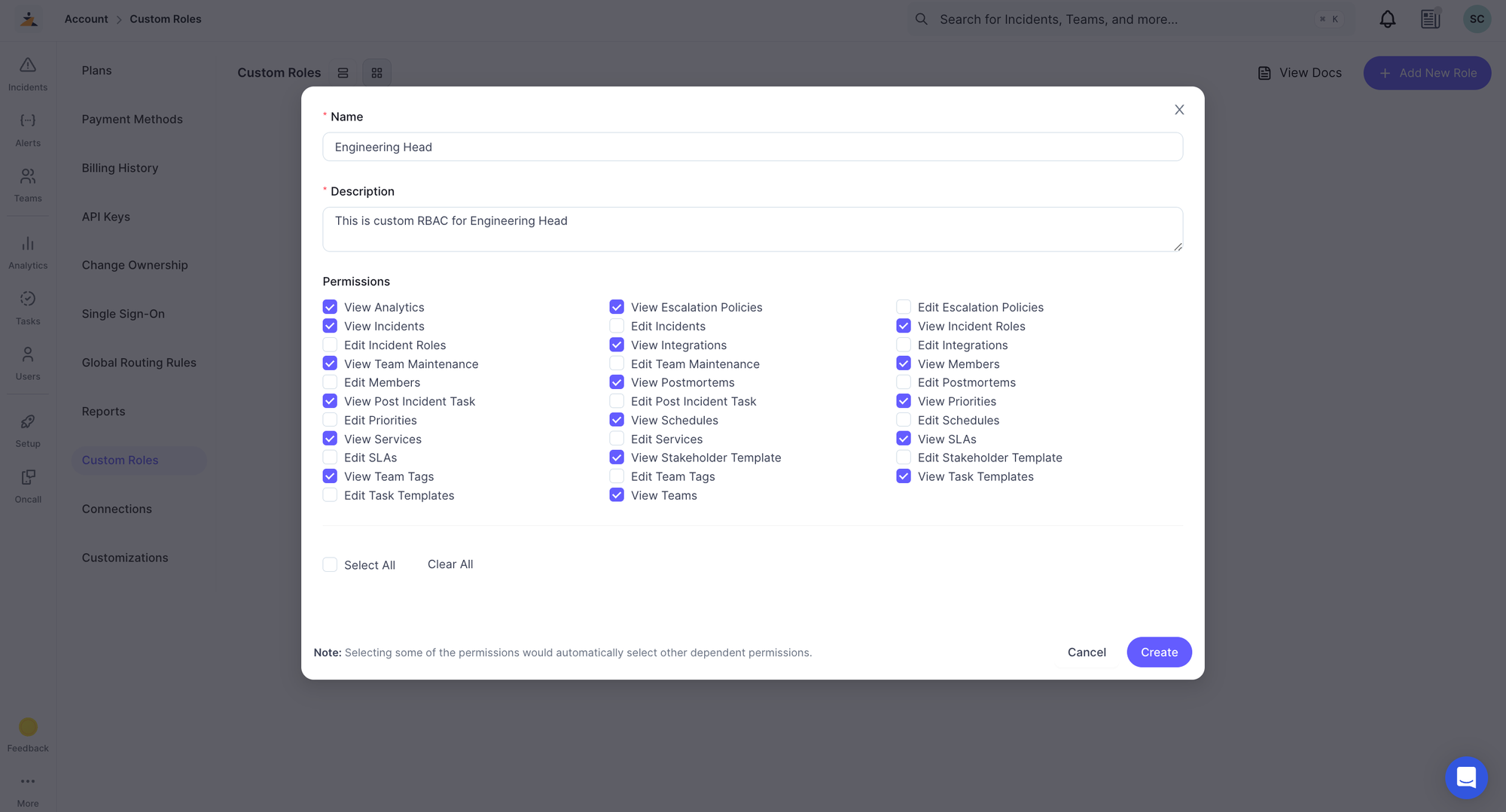

List of Account Level Permissions
Note: Selecting some permissions would automatically select others that the chosen permission requires.
Leveraging Alert Rules and RBAC together
With RBAC enabled, can also leverage Xurrent IMR Alert Rules to automatically Assign the incident to a User from another Team, Attach Escalation Policies from other teams and Add Global Users and On-Call Users from Global Schedules as responders to incoming incidents.
Before proceeding with building your alert rules, please ensure that the necessary permissions have been enabled for the teams and users which you want to be accessible via alert rules.
So to use the Route to Escalation Policy action, the Attach Escalation Policies permission should be enabled on the Account Level Access settings for the team to which the Escalation Policy belongs to.
To assign an incident to a user outside the team via alert rules, grant them a role with the Edit Incidents permission.
Example: Add the On-Call User from a Global Schedule as an Incident Responder
To enable this action, please make sure that the team with the incoming incident has the View Incident permission enabled, and the team to which the Schedule belongs to has the Attach Schedules and View Services permissions enabled on the Account Level Access settings.
- Click on the Service your Integration is in.
- Go to the Integrations tab and choose the integration for which you want to add an RBAC Alert Rule.
- Click on the Alert Rules tab from the secondary sidebar and then the Create Alert Rule button.
- Give your alert a name and set the conditions and actions as intended, an example is shown below. Save to apply.

Discover more Alert Rules use-cases and examples here.
















.jpg)